Starting today, you can take advantage of the new “age” grouping for the alert trends graph and explore enhanced filter options on the security overview dashboard, aimed at improving your analytical process and security management.
Security alert age trends
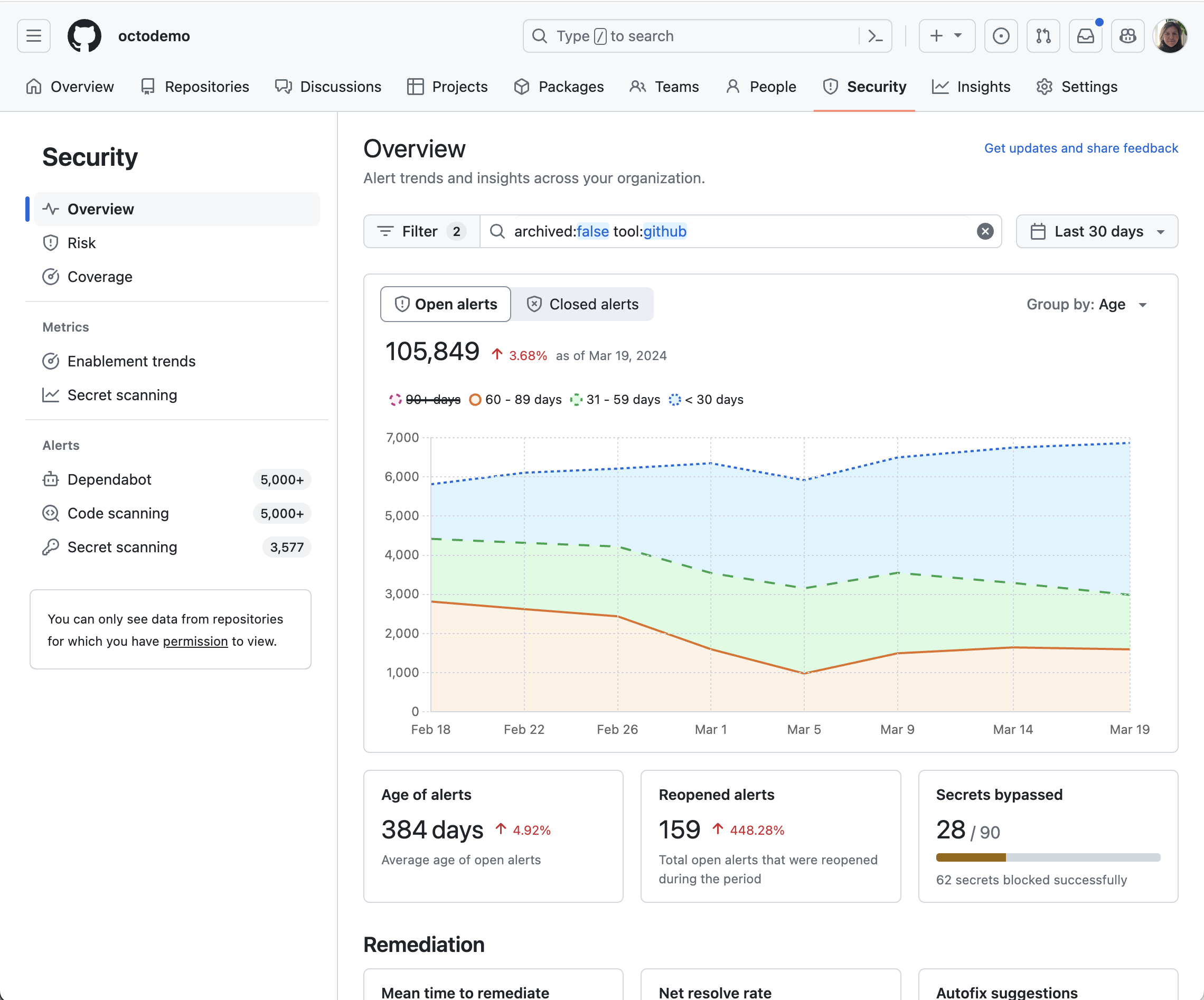
Explore the dynamics of your security alerts with the new alert age grouping on the alert trends graph. This new functionality offers a refined view into the lifecycle of your security alerts, enabling you to better evaluate the timeliness and effectiveness of your response strategies.
New filter options
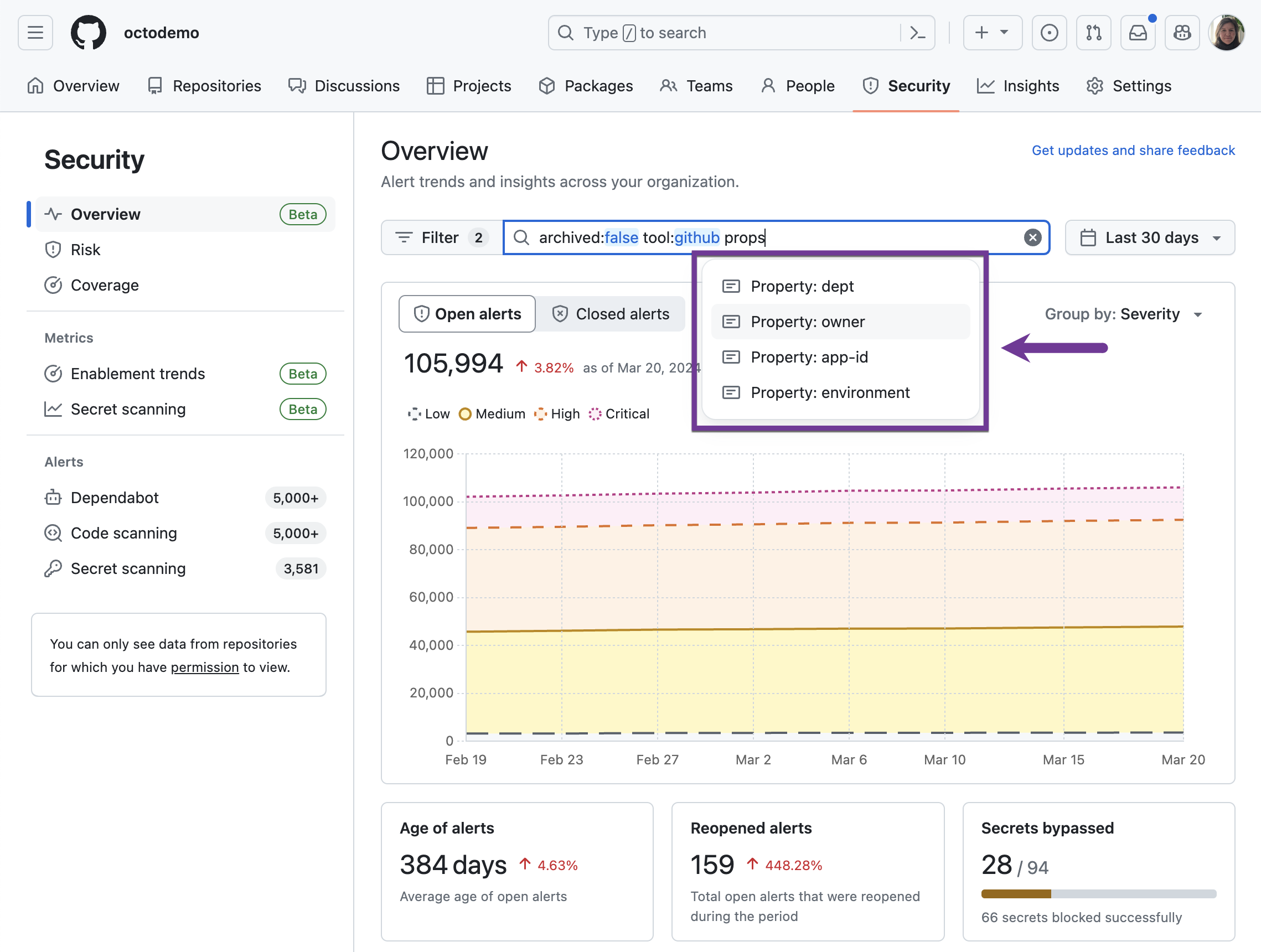
Leverage enhanced filters to fine-tune your security insights on the overview dashboard:
* Custom repository property filters: With repository custom properties, you can now tag your repositories with descriptive metadata, aiding in efficient organization and analysis across security overview.
* Severity filters: Severity-based filters allow you to concentrate on the vulnerabilities that matter most, streamlining the process of security risk assessment and prioritization.
* Improved date picker controls: Navigate through time with ease using the new date picker options, allowing for quick selection of rolling periods like “Last 14 days,” “Last 30 days,” or “Last 90 days.” Bookmark your preferred time window to keep your analysis current with each visit.
You can access these new functionalities in security overview by navigating to the “Security” tab at the organization level.
These features are now available as a public beta on GitHub Enterprise Cloud and will be available in GitHub Enterprise Server 3.13.
Learn more about security overview and send us your feedback

