Keeping secrets out of public repositories
With push protection now enabled by default, GitHub helps open source developers safeguard their secrets, and their reputations.
Accidental leaks of API keys, tokens, and other secrets risk security breaches, reputation damage, and legal liability at a mind-boggling scale. In just the first eight weeks of 2024, GitHub has detected over 1 million leaked secrets on public repositories. That’s more than a dozen accidental leaks every minute.
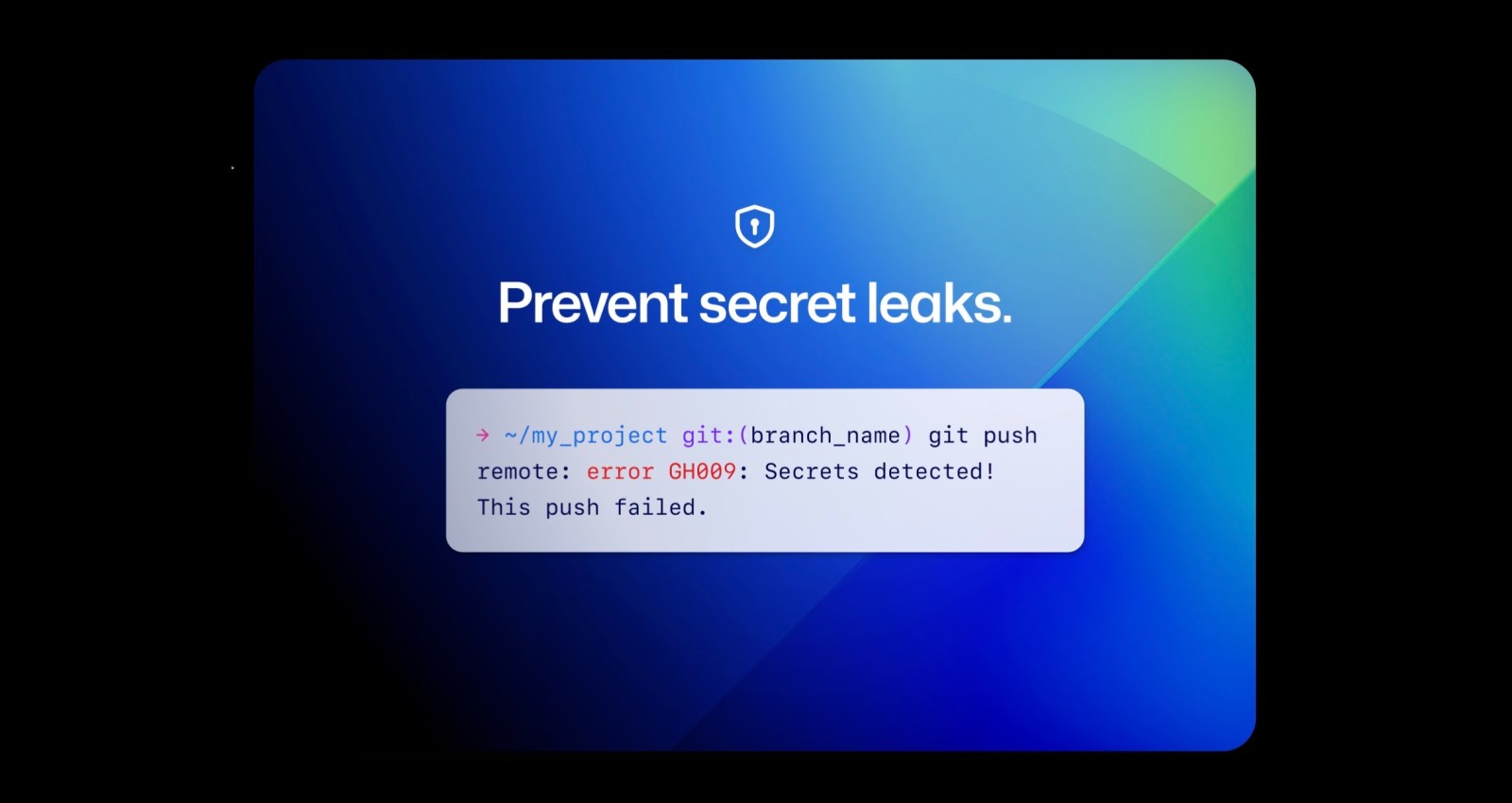
Since last August, all GitHub cloud users could opt-in to secret scanning push protection, which automatically blocks commits when a secret is detected. Now, we’ve enabled secret scanning push protection by default for all pushes to public repositories.
What’s changing
This week, we began the rollout of push protection for all users. This means that when a supported secret is detected in any push to a public repository, you will have the option to remove the secret from your commits or, if you deem the secret safe, bypass the block. It might take a week or two for this change to apply to your account; you can verify status and opt-in early in code security and analysis settings.
How will this change benefit me?
Leaked secrets can pose a risk to reputation, revenue, and even legal exposure, which is why GitHub Advanced Security customers scan more than 95% of pushes to private repositories. As champions for the open source community, we believe that public repositories–and your reputation as a coder–are worth protecting, too.
Do I have a choice?
Yes. Even with push protection enabled, you have the choice to bypass the block. Although we don’t recommend it, you can also disable push protection entirely in your user security settings. However, since you always retain the option to bypass the block, we recommend that you leave push protection enabled and make exceptions on an as-needed basis.
What about private repositories?
If your organization is on the GitHub Enterprise plan, you can add GitHub Advanced Security to keep secrets out of private repositories as well. You’ll also get all of the other features for secret scanning, along with code scanning, AI-powered autofix code suggestions, and other static application security (SAST) features as part of a comprehensive DevSecOps platform solution.
Learn more about secret scanning
GitHub secret scanning guards over 200 token types and patterns from more than 180 service providers, and boasts the industry’s highest precision and lowest rate of false positives.1 Together, we can keep secrets from leaking on public repositories.
- Learn more about secret scanning
- Learn more about push protection for users
- Join the discussion within GitHub Community
Notes
- A Comparative Study of Software Secrets Reporting by Secret Detection Tools, Setu Kumar Basak et al., North Carolina State University, 2023. ↩
Tags:
Written by
Related posts

Still a developer. Just outside. Our latest GitHub Shop collection is here.
The ESC collection lets you escape the confines of your desk and get out into the sun where good ideas are bound to happen.

Take your local GitHub sessions anywhere
Kick off work in VS Code or the CLI, finish it from your phone. Remote control for GitHub Copilot sessions is now generally available on github.com and GitHub Mobile.

GitHub availability report: April 2026
In April, we experienced 10 incidents that resulted in degraded performance across GitHub services.