What’s new from GitHub Changelog? October 2021 recap
A public beta of the new GitHub Issues, a “security manager” role for organizations, a command palette beta, and lots more.

A lot happened in the past month! Maybe you’ve been so busy diving into all the excellent GitHub Universe 2021 sessions that you missed some of the additional features we released in October. Don’t worry—we’ve got you covered. In this monthly recap, we will go over all of the announcements, starting with the new GitHub Issues experience.
What was big in October?
During Universe, we announced that we’re bringing the new GitHub Issues to public beta with some new added capabilities, such as converting a draft issue to an issue, running bulk action in tables and boards, automating repetitive action through workflows, and setting your team’s tempo with iterations. Check how we’re using the new GitHub Issues for our public roadmap and watch the interactive session to learn more.
We’re using the new GitHub Issues to track work on our public roadmap
In other big news, GitHub Codespaces is now generally available for GitHub Team and Enterprise Cloud accounts. You can now spin-up dev environments from your browser or through Visual Studio Code with Codespaces. Go ahead and try the new Codespaces features, such as the new devcontainer feature composition, GitHub CLI, and more.
Literally everything we shipped
General updates
At Universe, we announced the command palette beta, which allows you to execute commands from your keyboard: search for repositories, change themes, create issues, and more. It’s available to all Github.com users. Open the command palette on Windows and Linux with Ctl k or Ctl alt kand on Mac with ⌘ k or ⌘ option k.
That’s not all you can now do with your keyboard. We’ve added keyboard shortcuts for quotes and lists in Markdown files, issues, pull requests and comments.
- To add quotes:
cmd+shift+.on Mac orctrl+shift+.on Windows/Linux. - To add an ordered list:
cmd+shift+7on Mac orctrl+shift+7on Windows/Linux. - To add an unordered list:
cmd+shift+8on Mac orctrl+shift+8on Windows/Linux.
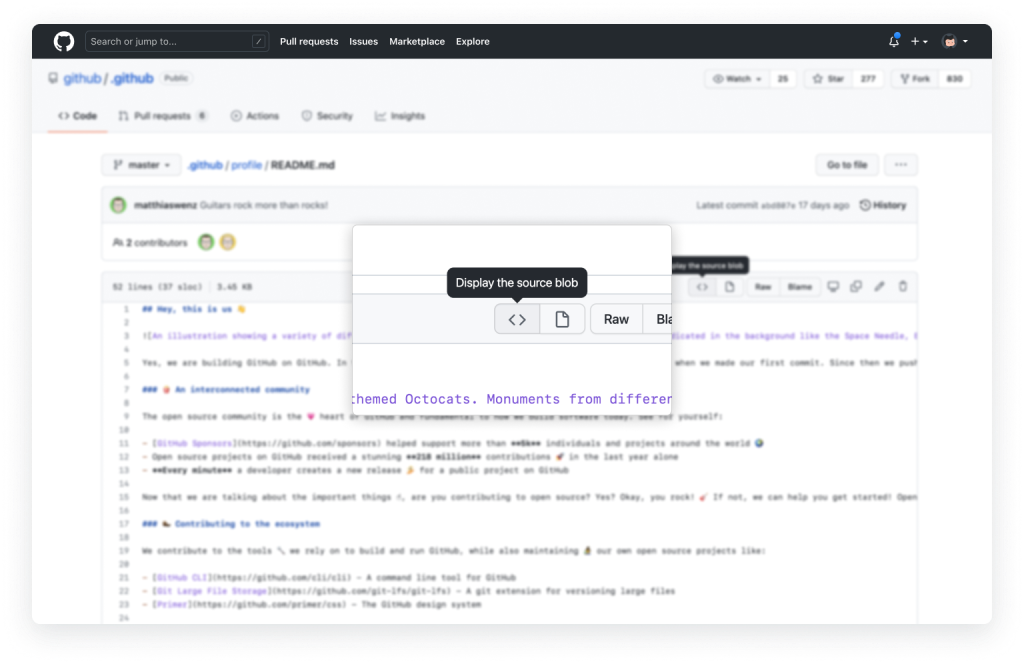
One new UI trick: toggle between source view and rendered Markdown view through the UI by clicking the button to “Display the source blob” at the top of any Markdown file.
A few smaller general announcements from October:
- We’ve added S3 support to the audit log streaming beta available to GHEC users.
- The GitHub App for Microsoft Teams can now alert you to more, like when a new release is published to a repository.
- Organization owners on GitHub.com and GHEC can now export a list of the organization’s members in JSON or CSV format.
GitHub Actions
A few months ago, we introduced the permissions key in the Actions workflow config, which enables you to control the permissions granted to a particular workflow or job. Workflows triggered by Dependabot pull requests now respect the permissions specified in your workflows, so you can control how you manage automatic dependency updates. Default token permissions remain read-only.
We’re excited about the public beta that lets you reuse entire workflows as if they were actions. Instead of copying and pasting workflow definitions across repositories, you can reference an existing workflow with a single line of configuration.
For secure cloud deployment, GitHub Actions now supports OpenID Connect (OIDC), which uses short-lived tokens that are automatically rotated for each deployment.
More granular personal access token scopes are now available for self-hosted runners in enterprises. You can use the manage_runners:enterprise scope instead of the admin:enterprise scope for your tokens.
Finally, the Windows 2016 runner image will be removed from GitHub-hosted runners on March 15, 2022.
GitHub API
You can now set whether a repository allows forking when creating or updating it using either the REST or GraphQL API.
The REST API header is no longer needed for the twenty-three REST API previews that have been graduated.
The Codes of Conduct API preview, which was accessible with the scarlet-witch-preview header, is being deprecated.
GitHub Enterprise Cloud
GHEC enterprise organizations now have access to custom repository roles (in beta). You can configure these roles from a set of 40+ fine-grained permissions based on your specific needs.
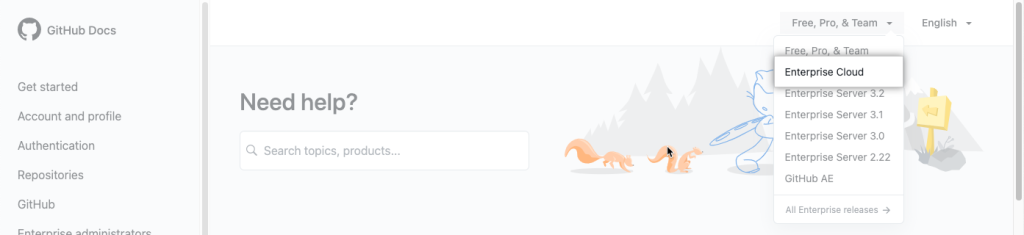
It’s also easier to get help when you need it. In GitHub Docs, you can now choose Enterprise Cloud from the “Version” drop-down to see content that aligns with the experience of using GitHub Enterprise Cloud.
GitHub Issues
In addition to the new public beta of GitHub Issues, we’ve been working on some quality-of-life improvements:
- Based on community feedback, closed issues now display a purple icon rather than a red one. No more fleeting panic about all the red in your closed issue queue!
- We’ve also improved notification email titles for issues and PRs. Titles now indicate
issue #xxorPR #xx.
GitHub Mobile
The Explore tab on GitHub Mobile has been redesigned to make it easier to find cool projects on GitHub, including personalized repository recommendations and trending projects.
npm
The npm advisory database is now part of the GitHub Advisory Database. npm audit will return URLs to the GitHub Advisory Database and the advisories on the npmjs.com will redirect to GitHub.
A couple of other changes: as previously announced, the npm registry now requires TLS 1.2 or higher for all requests, including package installation. We’ve also upgraded the npm CLI to version 8.
GitHub Pull Requests
We announced a limited beta for pull request merge queue during Universe. This feature enables the efficient merging of pull requests without the typical delays that exist between merges today. It works by validating, in parallel, different combinations of pull requests identified as “ready to merge.” Learn more, including how to apply.
The diff setting to hide whitespace changes in a pull request is now remembered. You no longer need to re-enable it when you switch to another tab, or when you come back to the same pull request later.
You can now use a fixed-width font in Markdown-enabled fields. These fields previously used a variable-width font, which can present challenges when you’re trying to edit advanced Markdown structures like tables and code snippets.
As mentioned earlier, we’ve improved notification email titles for issues and pull requests. Titles now indicate issue #xx or PR #xx.
GitHub Releases
Two improvements to the release process on GitHub are generally available:
- Maintainers can now automatically generate release notes!
- A UI refresh gives more clarity into what’s included in a given release and recognition for contributors in the community.
GitHub Repositories
It’s now easier to search branches by exact name. In the code browser, when a name exactly matches what you type in the search box, it moves to the top of the suggestion list.
Public repositories now have a public label next to their names like private and internal repositories do.
When a new tag is created, the push webhook payload will now always include a head_commit object that contains the data of the commit that the new tag points to.
GitHub Security
We’ve added Ruby support (beta) to the CodeQL engine that powers GitHub code scanning! Use it to spot common security issues like SQL injection, reflected cross-site scripting, and unsafe deserialization.
Dependency review is generally available! This security feature helps you understand dependency changes and the security impact of these changes when you’re reviewing pull requests.
Here’s a time-saver: if you draft a Security Advisory for a repository and the vulnerability impacts multiple packages, you can now identify all affected products in that advisory rather than having to draft multiple advisories.
Speaking of time-savers, organizations can now use the “security manager” role to grant entire teams the permission to manage security alerts and settings on repositories across the organization.
GitHub’s list of secret scanning partners grew again in October with the addition of Checkout.com and FullStory. Checkout.com is a cloud-based global payments platform that alerts customers and account managers of suspected credential compromise based on GitHub notifications. FullStory‘s Digital Experience Intelligence platform transforms digital interactions across websites and mobile apps into actionable metrics.
A few more security tidbits:
- A warning is now displayed when a file’s contents include bidirectional Unicode text, which can be interpreted or compiled differently than it appears in a user interface.
- The dependency graph now supports the Poetry package manager.
- We’re removing the pattern for Azure SQL connection strings from our default pattern set on private repositories.
GitHub Sponsors
For tax purposes, maintainers will now see the VAT status and location of their sponsors in transaction exports.
Take a look at our public roadmap for what’s coming next, follow GitHub Changelog on Twitter, and check back on the GitHub Blog for another recap next month.
Tags:
Written by
Related posts

GitHub Universe is back: All together now, in the agentic era
GitHub Universe is back: returning to the historic Fort Mason Center in San Francisco on October 28–29, 2026.

GitHub Copilot app: The agent-native desktop experience
At Microsoft Build 2026, GitHub introduced new tools, updates, and surfaces so agents can work the way you already work.

Still a developer. Just outside. Our latest GitHub Shop collection is here.
The ESC collection lets you escape the confines of your desk and get out into the sun where good ideas are bound to happen.