
3 common DevOps antipatterns and cloud native strategies that can help
Explore how GitHub and cloud native strategies can help you address common DevOps pipeline and team antipatterns.
GitHub Blog Search

Explore how GitHub and cloud native strategies can help you address common DevOps pipeline and team antipatterns.

Secret scanning emits audit log events for custom pattern push protection enablement

GitHub’s search inputs have several complex accessibility considerations. Let’s dive into what those are, how we addressed them, and talk about the standalone, reusable component that was ultimately built.
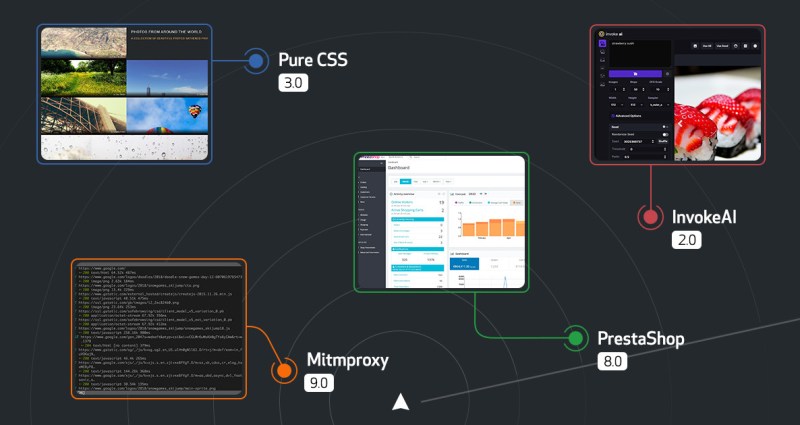
Before you say it, yes, the October Release Radar was supposed to be shared in November. But with Hackatoberfest, GitHub Universe, Turkey Day, and in real life (IRL) conferences returning…
Administrators, or enterprise owners, have the increased responsibility of managing their account and keeping it secure. We are excited to introduce what is new with enterprise accounts and what is coming soon.

Dependency review API is generally available with updates to dependency review enforcement

CodeQL code scanning now supports customizing build configurations for Go analysis

Secret scanning enterprise-level enablement events now in the audit log

Having a robust security plan is key to innovation. These tips will empower you to gain the upper hand on cyberattacks, so you can ship quickly and innovate with ease.

Secret scanning alerts now have a timeline and users can add a comment when resolving

As the home for developers, we understand the key role our communities play in steering digital transformation and maintaining societal infrastructure. That's why we choose to drive and support policies and initiatives like the Copenhagen Pledge on Tech for Democracy. We're committed to working with like-minded organizations, governments, and civil society to make digital technologies work for democracy and human rights, and we encourage you to join us in this pledge.

We’re reporting on a six-month period rather than annually to increase our level of transparency. For this report, we’ve continued with the more granular reporting we began in our 2021 reports.

Supply chain attacks exploit our implicit trust of open source to hurt developers and our customers. Read our proposal for how npm will significantly reduce supply chain attacks by signing packages with Sigstore.

In this post I'll exploit CVE-2022-1134, a type confusion in Chrome that I reported in March 2022, which allows remote code execution (RCE) in the renderer sandbox of Chrome by a single visit to a malicious site. I'll also look at some past vulnerabilities of this type and some implementation details of inline cache in V8, the JavaScript engine of Chrome.
Expand the completeness of your dependency graph by using the dependency submission API, which will create more comprehensive alerts on supply chain vulnerabilities

Dependency graph has a REST API for submitting dependencies detected at build time

Secret scanning push protection bypasses are now shown in the audit log and API