Justin Hutchings
Director of Product Management for supply chain security. I manage the team that's behind Dependabot, the Advisory Database, and the dependency graph. Twitter: https://twitter.com/jhutchings0
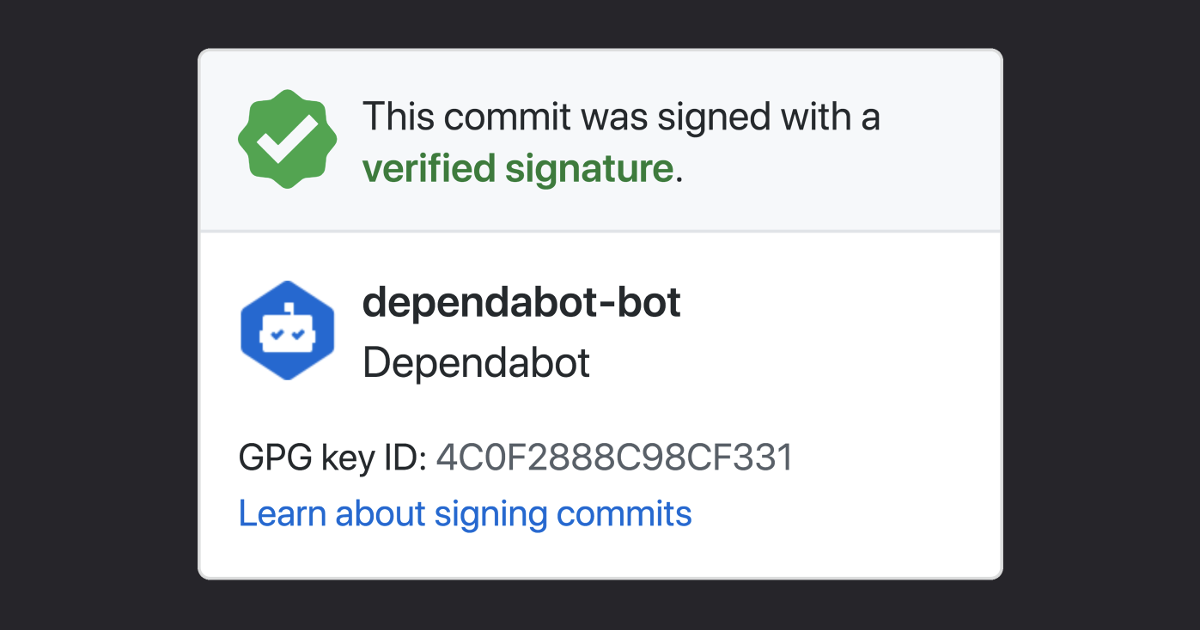
Commit signing is now enabled for all bots by default.
Businesses and open source projects alike want to be sure that a commit is from a verified source—whether it’s from a developer across the world or a bot that’s integrated into their workflow.
GitHub has supported GPG signature verification for human-authored commits for a while, but bots like Dependabot are becoming an increasingly important part of our workflows. That changes now—bot commit signing has been enabled for all bots by default.

Commit signing allows a user (or bot) to cryptographically vouch for the integrity of the commit, and that they authored it. If a commit or tag has a GPG or S/MIME signature that is cryptographically verifiable, GitHub marks the commit or tag as verified with a big green checkmark ✓.
Find out more about commit signature verification
Did you know? Support for commit signing was introduced in January 2012 when v1.7.9 was released. We introduced support on GitHub.com back in April 2016.

How the GitHub Issues team used client-side caching, smart prefetching, and service workers to make navigation feel instant.

Learn how Github uses eBPF to detect and prevent circular dependencies in its deployment tooling.

The path to better performance is often found in simplicity.