Prioritize security alerts with runtime context from Dynatrace
You can now use runtime context from Dynatrace to prioritize GitHub Advanced Security alerts based on deployed artifacts and runtime risk in your Kubernetes environment.
When you connect Dynatrace to GitHub, you’ll see deployment context for container images that Dynatrace maps to your repositories, along with runtime risk signals. You can use this context to focus remediation on alerts that affect deployed artifacts, especially when Dynatrace detects higher-risk runtime conditions.
How to use runtime context in GitHub
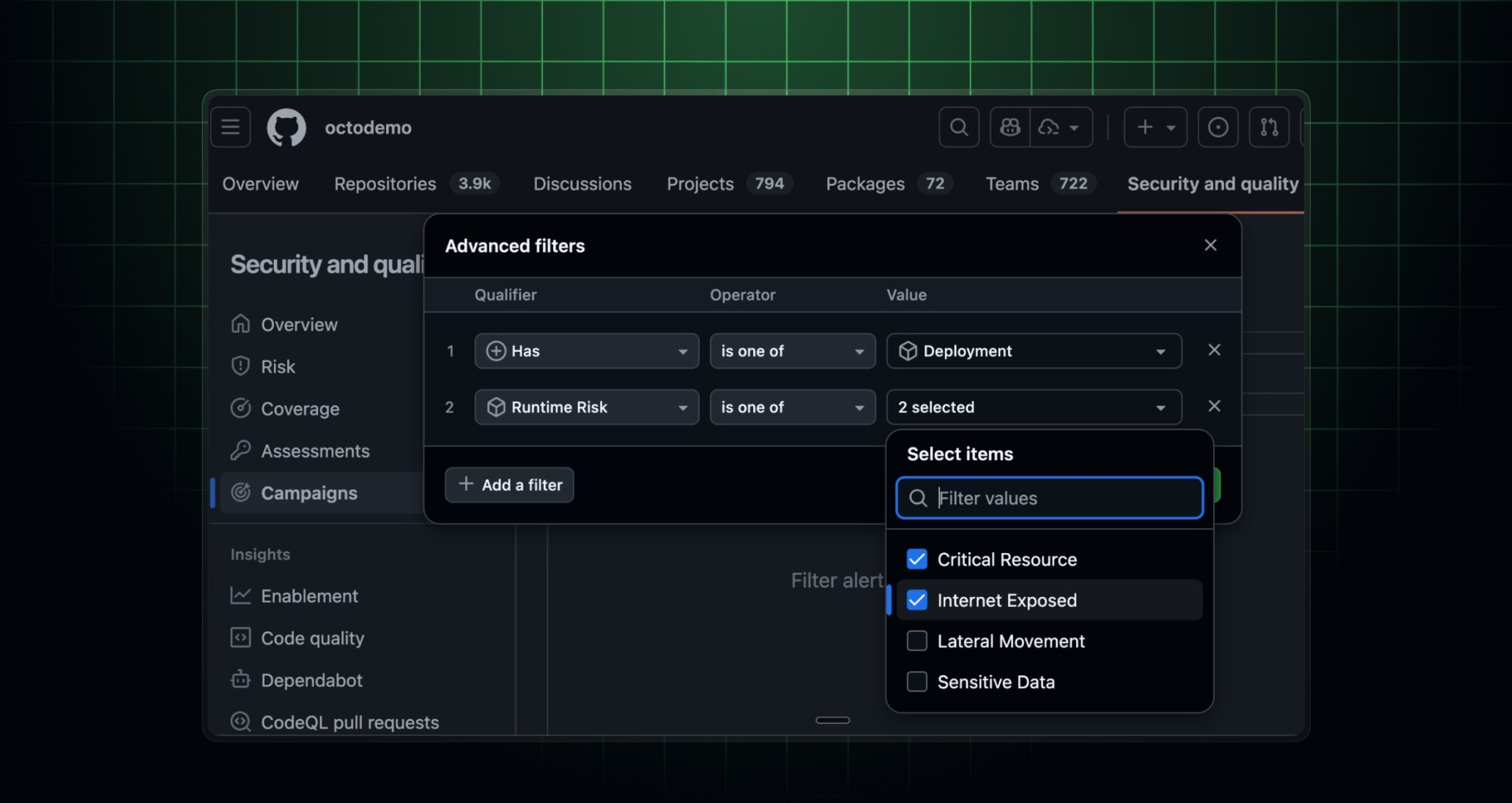
You can use deployment visibility and runtime risk signals to filter and prioritize GitHub code scanning and Dependabot alerts, both on the alert pages and in security campaigns. For example, you can filter a large list down to just those vulnerabilities that affect deployed artifacts and are exposed to the internet:
has:deployment AND runtime-risk:internet-exposed
Runtime risk signals include:
- Public internet exposure (
runtime-risk:internet-exposed). - Access to sensitive data assets (
runtime-risk:sensitive-data).
Availability
This feature is generally available for GitHub Enterprise Cloud customers.
To learn how to configure the Dynatrace integration with GitHub Advanced Security, see Dynatrace’s documentation.