ICYMI: CodeQL enhancements
Learn about CodeQL’s improved user experience and enhancements that let you scan new languages, detect new types of CWEs, and perform deeper analyses of your applications.
Over the last year, GitHub has brought a number of enhancements to CodeQL, the semantic analysis engine that powers code scanning. You can now scan new languages, detect new types of CWEs, perform deeper analyses of your applications, and enjoy improvements to the user experience. Let’s check out some of these major enhancements to CodeQL and learn how you can take advantage of them in your environment.
Test new ecosystems
Have you tried scanning your Ruby codebases? We announced the general availability of Ruby support for CodeQL at GitHub Universe 2022. We’ve made a number of improvements since our beta, including doubling the number of default queries, providing coverage for all Ruby-related OWASP categories out-of-the-box, and optimizing performance to deliver tests in less than five minutes for 90% of beta users. To date, users scanning their Ruby codebases have fixed over 4,000 alerts, and on an average day we run almost 5,000 Ruby analyses.
Ruby has been a vital part of our SDLC for many years, as it allows us to build flexible applications to meet our evolving needs. The ability to scan Ruby codebases and identify and remediate vulnerabilities all within GitHub means that our developers are able to secure their code without disrupting their workflow.
You can also test your mobile applications with the beta of Kotlin support for CodeQL! CodeQL now natively supports Kotlin and mixed Java and Kotlin projects. Kotlin support is an extension of our existing Java support, and benefits from all of our existing CodeQL queries for Java, for both mobile and server-side applications.
Kotlin marks our first investment in mobile application security, and beta support for Swift will be coming later this year.
That isn’t to say you can only take advantage of testing for new languages. We’ve also made improvements to our current language support, including:
- Full support for Java 19
- Full support for Go 1.19
- Build support for C#11
- Full support for Python 3.11
All of this means that you can scan even more of the languages you use every day, to ensure your applications ship securely.
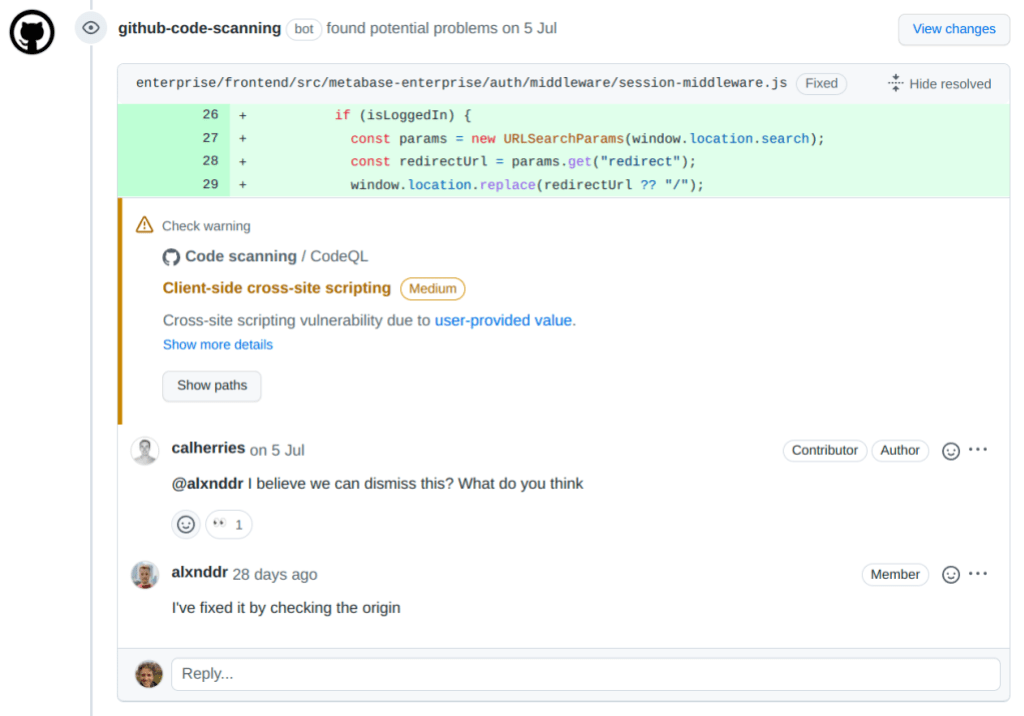
Perform deeper analysis of your code
Code scanning uses CodeQL queries to detect security vulnerabilities. The use of queries might sound complex, but we make it easy by providing out-of-the-box queries, written and curated by GitHub researchers and community security researchers, covering everything from the most critical to common vulnerabilities. We also give developers the ability to write custom queries in order to check for specific bugs or vulnerabilities that may have caused them problems in the past.
We’ve added a number of new queries to help you easily take advantage of CodeQL’s analysis capabilities. CodeQL now ships with 318 default security queries, an increase of 27% from last year, with the option to enable up to 432 with the extended query pack.
Together with Dependabot alerts, these queries cover all applicable OWASP categories, 100% of SANS CWE Top 25, and 100% of WASC’s applicable categories. This not only means that security teams can be confident that CodeQL is detecting the most critical vulnerabilities, but that developers can review them right in the pull request.
For a full list of CWE-based coverage, please see our CodeQL CWE coverage page. You can also check out our supported languages and frameworks page, which contains all updates to libraries and frameworks, along with links to the queries changelog for each language.
Seamlessly use CodeQL
Finally, we’ve made a number of improvements to the experience of using CodeQL. We added CodeQL pack support to code scanning, allowing you to leverage CodeQL packs in GitHub.com and GitHub Enterprise. We also launched the ability to customize CodeQL analysis using query filters. This gives you the flexibility to filter out particular checks that may not be relevant for your code base, allowing you to see more precise results for what security checks are most relevant. We’ve even improved the speed that CodeQL can run analyses by 16%, without compromising our best-in-class precision and low false-positive rate.
For security researchers, we’ve created and stored CodeQL databases for some of the most popular open source projects. These databases are easily obtainable through the CodeQL extension for VS Code to streamline writing and running CodeQL custom queries whilst performing security research.
The GitHub community has also been a key factor in the success of CodeQL, with users sharing resources and knowledge, and contributing to the development of the platform. For instance, the GitHub community was instrumental in helping add new out-of-the-box queries to analyze your codebase for security risk this year.
These new features and integrations have made it easier for developers to build secure code from the beginning, and for security researchers to catch vulnerabilities before they become a problem.
Get started with CodeQL
If you’re looking to get started with CodeQL and code scanning on your repository, you can easily enable it with our new default setup option. As always, CodeQL is free to use on open source repositories. If you’re looking to leverage CodeQL on private repositories, you can add on GitHub Advanced Security to your GitHub Enterprise subscription. Contact sales to learn more.
We’re always looking for ways to improve the products, so drop your comments in this repo to help us improve CodeQL for you and the community.
Tags:
Written by
Related posts
GitHub availability report: March 2026
In March, we experienced four incidents that resulted in degraded performance across GitHub services.

GitHub Universe is back: We want you to take the stage
Get inspired by five of the most memorable, magical, and quirky Universe sessions to date.

What’s coming to our GitHub Actions 2026 security roadmap
A look at GitHub Actions’ 2026 roadmap, outlining how secure defaults, policy controls, and CI/CD observability harden the software supply chain end to end.