Justin Hutchings
Director of Product Management for supply chain security. I manage the team that's behind Dependabot, the Advisory Database, and the dependency graph. Twitter: https://twitter.com/jhutchings0
It’s more important than ever that every developer becomes a security developer—that they responsibly disclose vulnerabilities and patch vulnerable code quickly. Today, we’re excited to announce several new security features designed to make it easier for developers to secure their code.

We’re all part of a deeply interconnected community, where the software we write builds on the work of others. Ninety-nine percent of new software projects depend on open source code. This extensive code reuse helps everyone build better software faster than ever before, but it also puts us all at risk of distributing security vulnerabilities from our dependencies. It’s more important than ever that every developer becomes a security developer—that they responsibly disclose vulnerabilities and patch vulnerable code quickly.
Today, we’re excited to announce several new security features designed to make it easier for developers to secure their code.
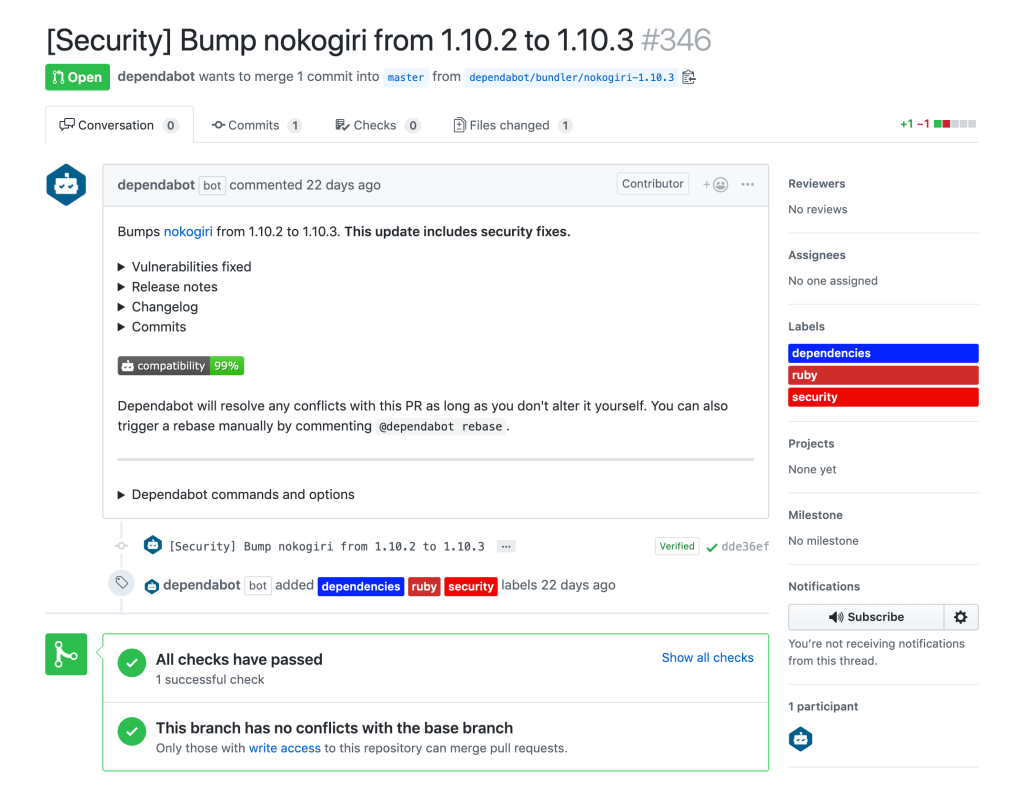
While security vulnerability alerts provide users with the information to secure their projects, industry data shows that more than 70 percent of vulnerabilities remain unpatched after 30 days, and many can take as much as a year to patch! At GitHub, we want to give you the tools to make dependency upgrades easy, so we’re excited to announce that we’ve acquired and integrated Dependabot into GitHub. With the help of Dependabot, GitHub will monitor your dependencies for known security vulnerabilities and automatically open pull requests to update them to the minimum required version. We’ll be rolling out automated pull requests to all accounts with security alerts enabled over the coming months.
Nearly every software project will have a security bug at some point in its lifetime, but vulnerabilities in open source software can have a significant impact when thousands of projects depend on it. While major vendors may have a dedicated security team that knows how to work through security issues when they happen, most open source projects don’t. We’re excited to announce these new features to help maintainers privately address and responsibly disclose security issues.
The security challenges facing today’s software are community problems. With the breadth of data and connections GitHub maintains as the leading software development platform, we have a responsibility to protect the community from threats and enhance security for everyone. We’re continuing to invest in new capabilities and work with partners to bring industry best practices into GitHub.
We are committed to empowering every developer by building an open, secure, and AI-powered platform that defines the future of software development.

Agentic workflows that run on every pull request can quietly accumulate large API bills. Here’s how we instrumented our own production workflows, found the inefficiencies, and built agents to fix them.
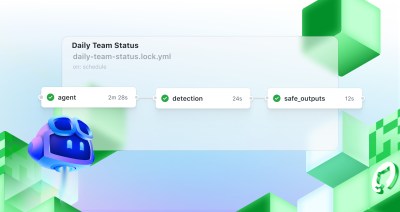
Discover GitHub Agentic Workflows, now in technical preview. Build automations using coding agents in GitHub Actions to handle triage, documentation, code quality, and more.