GitHub Advanced Security: Secret scanning for private repositories now available in limited public beta
GitHub has scanned public repositories for secrets (like API keys and tokens) for several years. Secret scanning protects our partners and our customers from unauthorized use of the services protected by those secrets. Just this month, 8% of active GitHub repositories committed a secret that was caught by secret scanning.
At GitHub Satellite, we announced secret scanning for private repositories, part of GitHub Advanced Security. We’re bringing the same lightning-fast scanning engine and broad set of 24 partners (including all the major cloud providers and many common SaaS providers) to your private repository, so you can catch secrets as soon as they’re checked in. Repository admins will be notified about any commit that contains a secret, and can quickly view all detected secrets in the repo’s Security tab.
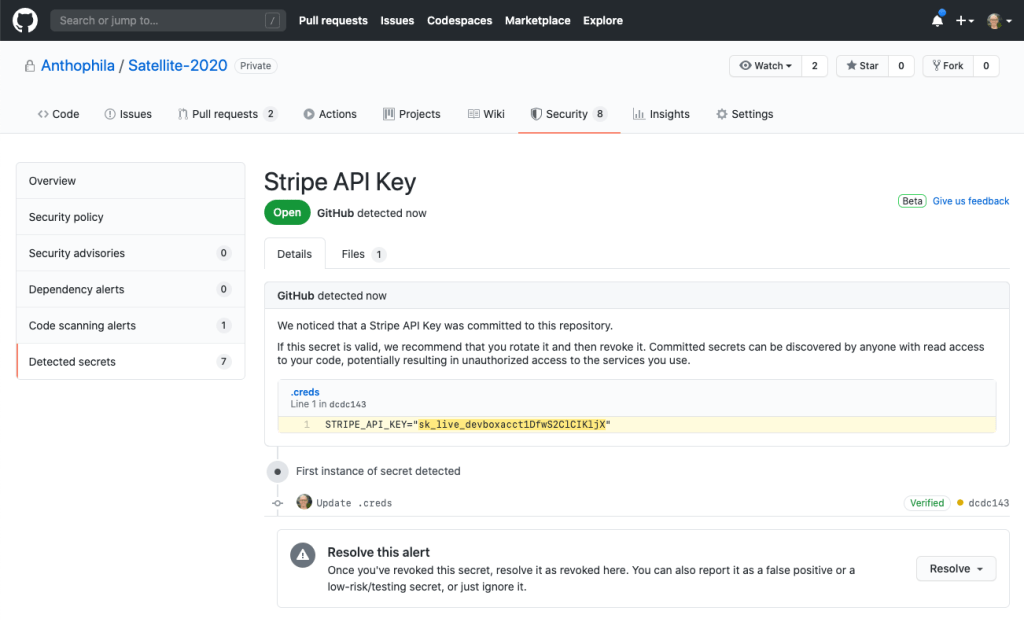
Secret scanning for private repositories is in limited public beta for Enterprise Cloud customers, and we expect to bring it to Enterprise Server by the end of 2020. This feature is part of GitHub Advanced Security for GitHub Enterprise customers.
Want to get started? Sign up for the beta, which includes secret scanning for private repositories and code scanning. If you’re a SaaS provider with secrets that you’d like GitHub to scan for, see our partnership docs for how to get started.
