GitHub Advanced Security: Introducing security overview beta and general availability of secret scanning for private repositories
GitHub Advanced Security helps you create secure applications with a community-driven, developer-first approach. Today, we are excited to announce two updates: Beta of the new security overview for organizations and…

GitHub Advanced Security helps you create secure applications with a community-driven, developer-first approach. Today, we are excited to announce two updates:
- Beta of the new security overview for organizations and teams, which provides a high-level view of the application security risks a GitHub organization is exposed to.
- General availability of secret scanning for private repositories, which has expanded coverage to include more than 35 partners.
Introducing the security overview for organizations and teams
GitHub’s security features provide developers with powerful tools for finding and remediating application security risks, but what if you’re an application security team or development leader responsible for hundreds or even thousands of repositories? This is where the new security overview on the Security tab of organizations and teams comes in.
GitHub Advanced Security customers now have a single place to see the application security risks detected by code scanning, Dependabot, and secret scanning. The security overview shows both these known security risks as well as where you have unknown risks because security features haven’t been configured.
Administrators can now see the GitHub security features that have been enabled and insights into what they discovered on the Security tab on organizations. To help you know where to start, we assign each repository a risk category based on the number and severity of active alerts.
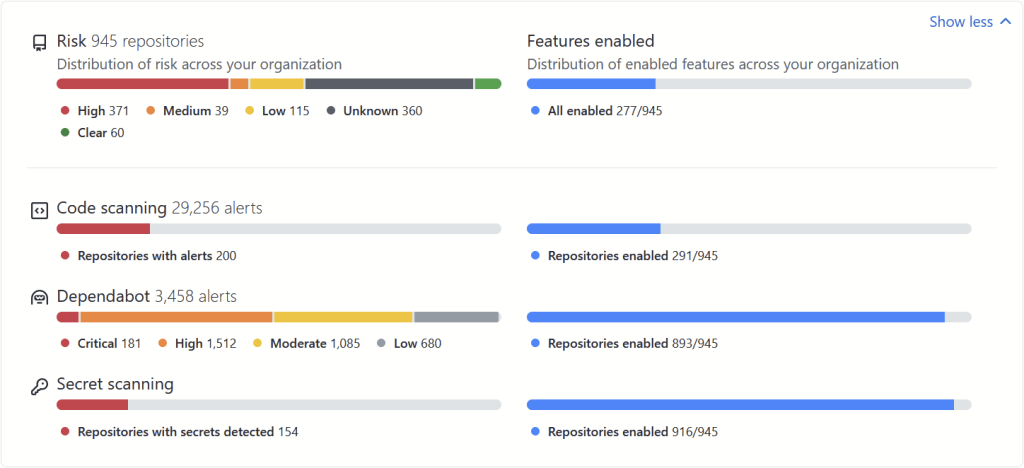
With our comprehensive set of filters, you can focus on just the repositories you care about. If you’re only interested in certain repositories, such as high-risk public repositories that have Dependabot alerts, you can limit your view to just those.
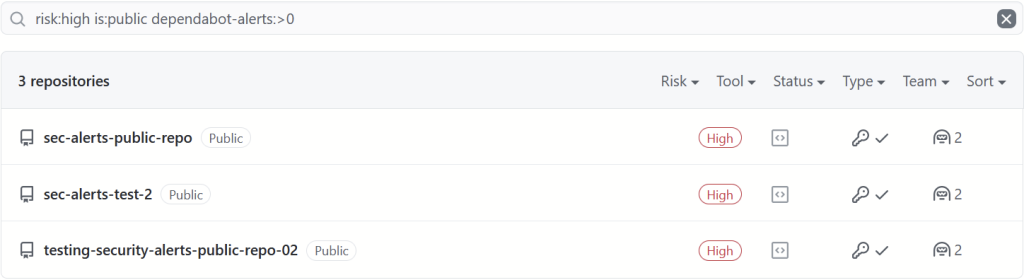
You can also see the individual repositories, the risk category they’ve been assigned, which security features are enabled on them, and how many active alerts they have. From here you can quickly drill into the repository to turn features on or view the alert details to take action.
It is important for developers and managers to have these same insights for the repositories they’re responsible for, so if your organization uses teams to manage repository access we also provide these insights to team members on the Security tab of their GitHub Team.
Secret scanning for private repositories is now generally available
We’ve been maturing and expanding secret scanning for private repositories since we announced it in beta in May 2020. Since then we’ve:
- Expanded secret scanning’s pattern coverage to cover tokens from more than 35 partners
- Added an API and webhooks for secret scanning alerts
- Started sending notifications to commit authors (as well as admins) when they commit secrets
The above are available now on GitHub Enterprise Cloud, and will all be included in GitHub Enterprise Server 3.1. We have more improvements planned for secret scanning for private repositories, including support for custom patterns, but it’s already helped organizations find and revoke over 5,000 exposed secrets. We’re excited to mark it as generally available.
Learn more and get started with GitHub Advanced Security
- Learn more about the new security overview and secret scanning in the GitHub Docs.
- The new security overview and secret scanning for private repositories are both part of GitHub Advanced Security. Find out more about how GitHub helps you ship secure applications, or contact Sales to discuss enabling Advanced Security on your account.
Tags:
Written by
Related posts

GitHub Universe is back: All together now, in the agentic era
GitHub Universe is back: returning to the historic Fort Mason Center in San Francisco on October 28–29, 2026.

GitHub Copilot app: The agent-native desktop experience
At Microsoft Build 2026, GitHub introduced new tools, updates, and surfaces so agents can work the way you already work.

Still a developer. Just outside. Our latest GitHub Shop collection is here.
The ESC collection lets you escape the confines of your desk and get out into the sun where good ideas are bound to happen.