
Audit log streaming to AWS S3 integration with AWS CloudTrail Lake
Audit log streaming to AWS S3 integration with AWS CloudTrail Lake
GitHub Blog Search

Audit log streaming to AWS S3 integration with AWS CloudTrail Lake

Twilio Segment is now a GitHub secret scanning partner

Secret scanning users can now see the validity of detected GitHub tokens

False-alert flags will appear in audit logs due to a bug in branch protections
GitHub now tells you whether GitHub tokens found by secret scanning are active so you can prioritize and escalate remediation efforts.
Git users are encouraged to upgrade to the latest version, especially if they use `git archive`, work in untrusted repositories, or use Git GUI on Windows.

Explore how GitHub and cloud native strategies can help you address common DevOps pipeline and team antipatterns.

Security overview's team filter now includes repositories with write privileges
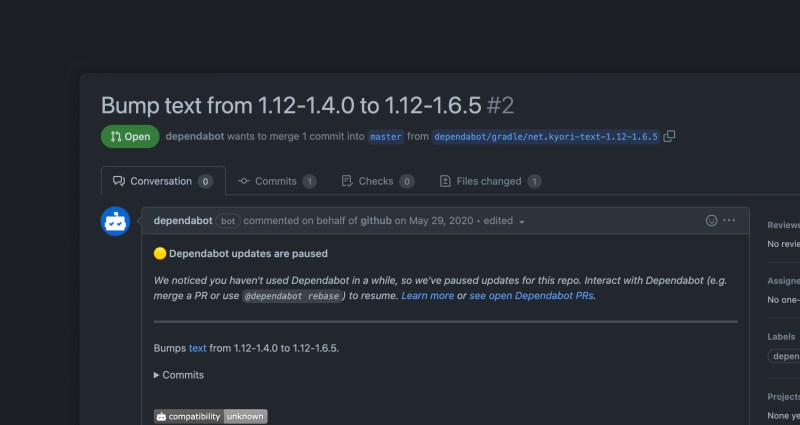
Dependabot is getting a little smarter—and, a little quieter—by reducing bot-based noise from repositories based on your interaction with Dependabot.

Discovering passwords in our codebase is probably one of our worst fears. But what if you didn’t need passwords at all, and could deploy to your cloud provider another way? In this post, we explore how you can use OpenID Connect to trust your cloud provider, enabling you to deploy easily, securely and safely, while minimizing the operational overhead associated with secrets (for example, key rotations).

Now, you can standardize and enforce CI/CD best practices across all repositories in your organization to reduce duplication and secure your DevOps processes.

GitHub Actions - Support for organization-wide required workflows public beta

Default setup is a new way to automatically set up code scanning on your repository, without the use of a .yaml file.

Code scanning can be set up more easily without committing a workflow file to the repository

Secret scanning emits audit log events for custom pattern push protection enablement