Credential revocation API now supports GitHub OAuth and GitHub app credentials
We’ve extended the Credential revocation API to support additional token types, enabling you to programmatically revoke any exposed credentials found on repositories or elsewhere. This helps you quickly limit the impact of credential exposure and improve the security of the software ecosystem.
You can now submit a bulk revocation request to revoke compromised or exposed tokens that you found on repositories, even if they aren’t yours.
This unauthenticated API is available for all users on github.com and supports these credential types:
- Personal access tokens (classic)
- Fine-grained personal access tokens
- OAuth app tokens
- GitHub App user-to-server tokens
- GitHub App refresh tokens
When the API receives a valid token, it automatically revokes the token and logs the revocation in the token owner’s security log. If the exposed token had access to a GitHub organization, that access is immediately removed. GitHub can’t reactivate any credentials that have been revoked; the token owner will need to generate new credentials.
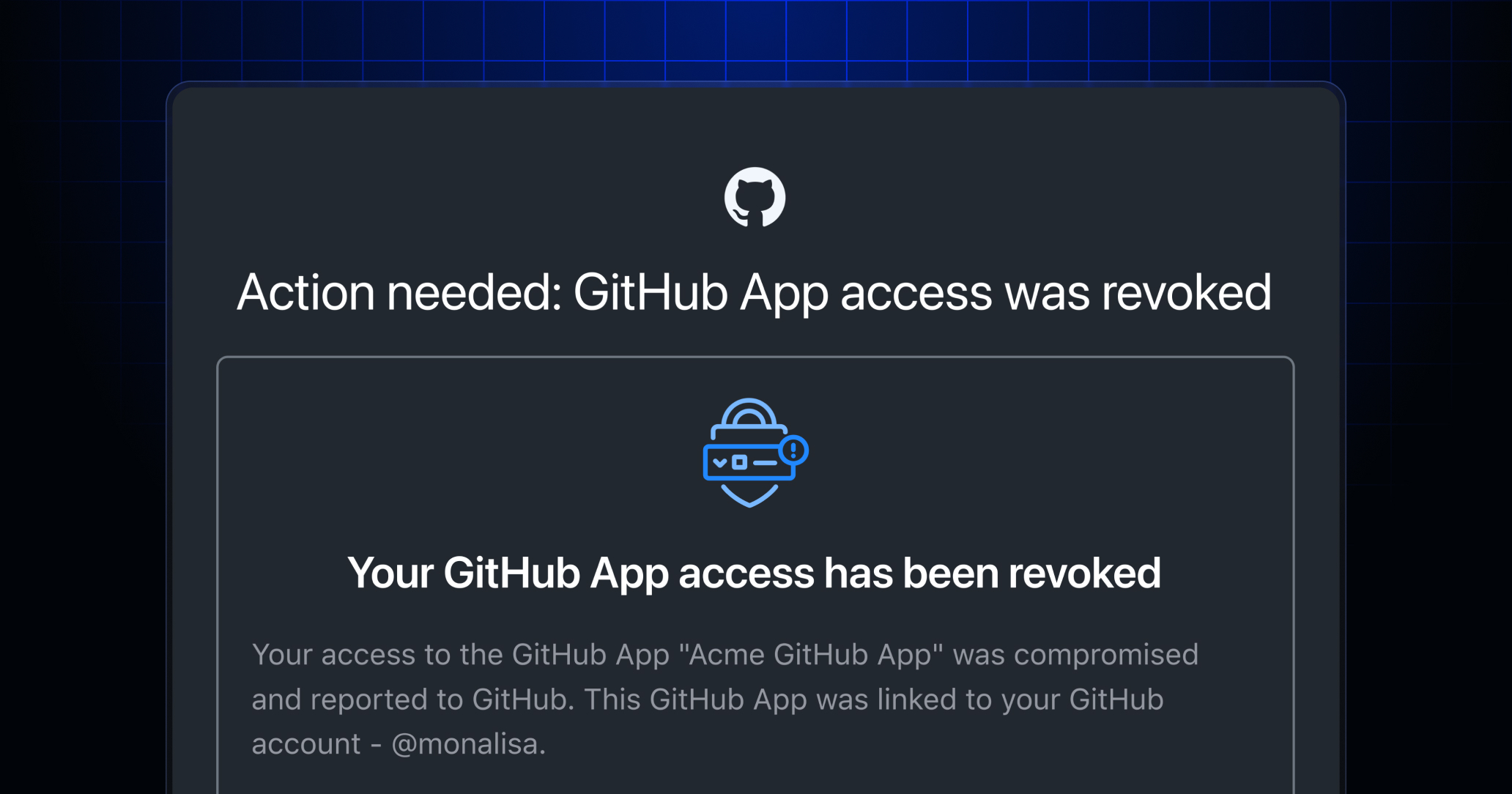
The API also notifies the token owner of the revocation through an email sent to the primary email address associated with the owner’s GitHub user account
To prevent abuse, this API is limited to 60 unauthenticated requests per hour and a maximum of 1,000 tokens per API request.
Join the discussion within GitHub Community.