Actions OIDC tokens now support repository custom properties
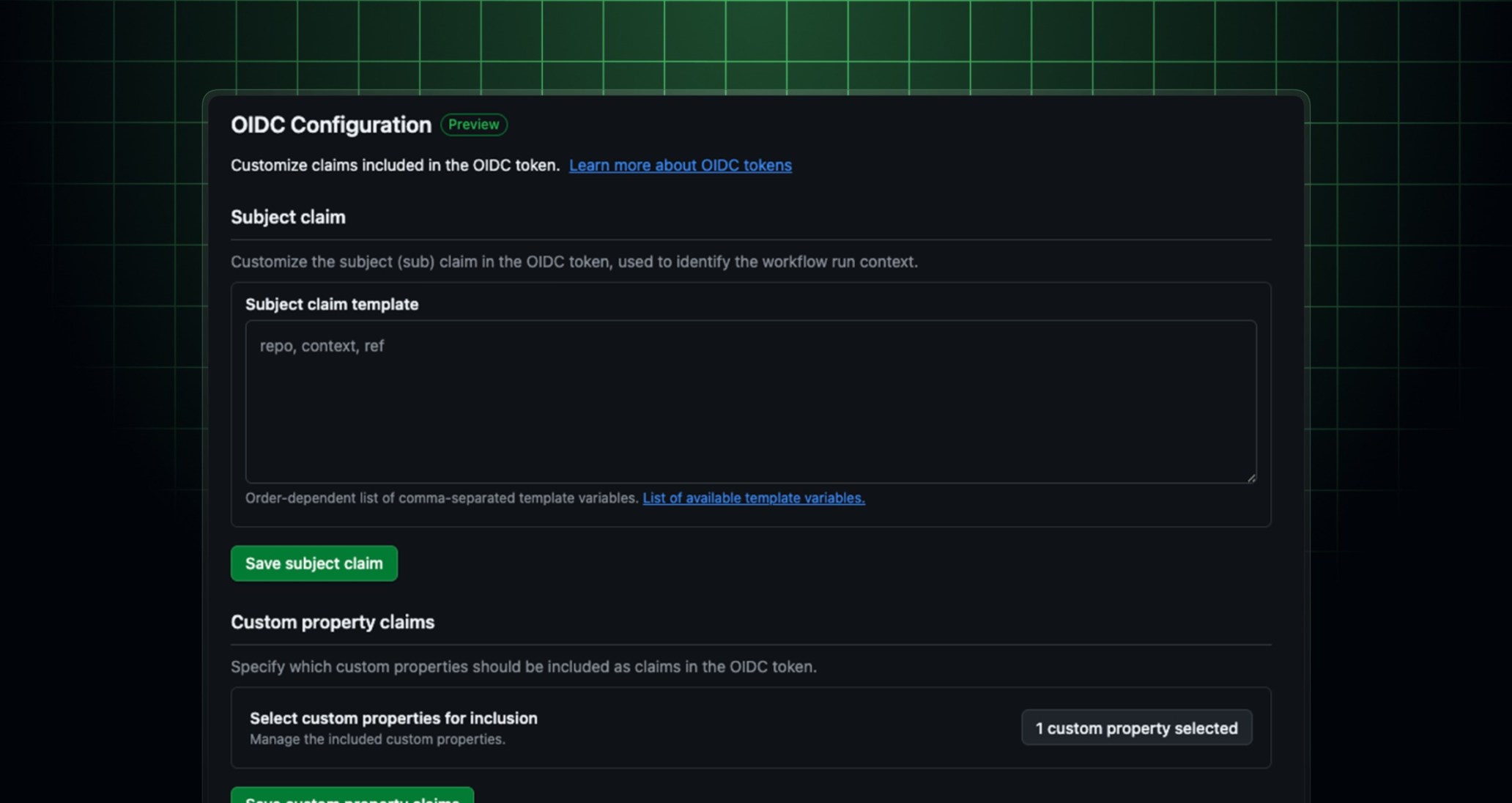
GitHub Actions OpenID Connect (OIDC) tokens now support repository custom properties as claims. Additionally, a new settings page is available in public preview, making it easy to configure OIDC token claims directly from your repository, organization, or enterprise settings while adding properties to the claim.
Organization and enterprise admins can select custom properties to include in OIDC tokens. Once a property is added to the claim, every repository with that property value set will automatically include it in its OIDC tokens, prefixed with repo_property_. You can use these claims to build attribute-based access control (ABAC) policies in Azure, AWS, GCP, and other cloud providers without modifying individual workflows.
With custom properties in OIDC tokens, you can:
- Eliminate duplication: Your governance metadata lives in one place and flows automatically into your cloud policies.
- Reduce configuration drift: Policies bind directly to repository attributes, so they stay accurate as your organization evolves.
- Accelerate onboarding: New repositories automatically inherit the right access policies based on their properties.
- Create consistent cross-cloud policies: Turn your existing GitHub metadata into an actionable control surface for managed identities across AWS, Azure, GCP, and beyond.
What you can do today
- Add repository custom properties to the OIDC token via the API or the new settings UI.
- Use custom properties in the subject claim for flexible policy targeting.
- View and manage OIDC token claim configuration from a new UI at the repository, organization, and enterprise level.
You can then reference this claim in your cloud provider’s trust policy to control access based on repository attributes. No static allow lists or per-repository workflow changes required.
To learn more, see Customizing the OIDC token.