Build Copilot Extensions faster with skillsets
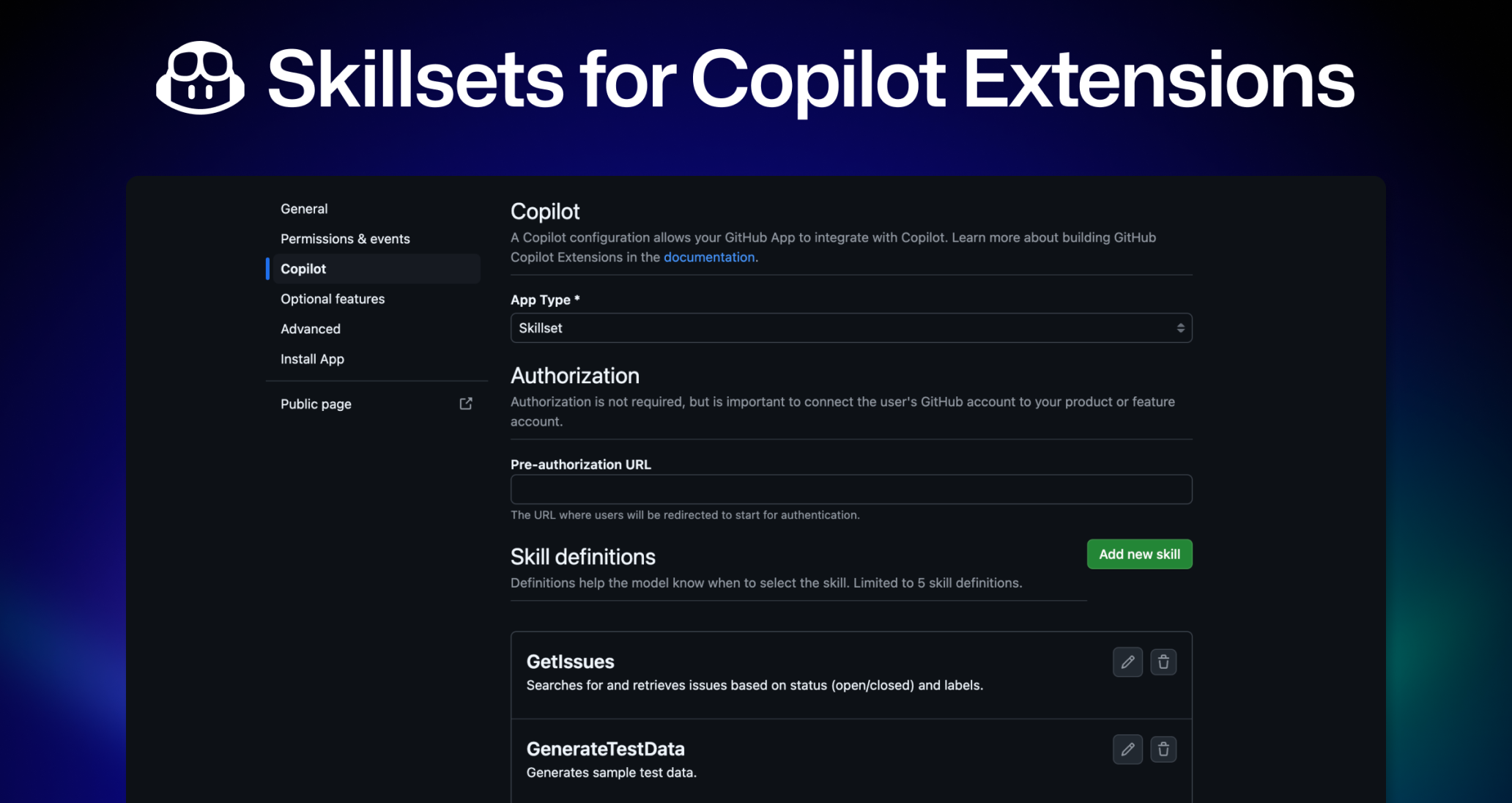
Today we’re introducing skillsets, a new lightweight way to build GitHub App-based Copilot Extensions alongside our existing agents approach. While agents offer full control over the user interaction, skillsets make it easy to integrate external tools and services into Copilot Chat by defining simple API endpoints – no AI expertise needed!
What’s new ✨
- Let Copilot handle all AI interactions and response formatting
- Define up to 5 skill endpoints that Copilot can call
- Simple JSON schema configuration
- Quick setup with minimal code
Benefits for builders ⚡️
- Faster Development: Focus on your core functionality instead of AI interactions
- Simple Implementation: Just define API endpoints, without managing LLM logic
- Minimal Setup: No complex server infrastructure required, with the option to use existing APIs
- Consistent Experience: Copilot maintains natural chat interactions automatically
Choosing your integration path 🛠
- Skillsets: Perfect for straightforward integrations like data retrieval and basic actions. You provide the API endpoints, and Copilot handles workloads like prompt crafting and response generation.
- Agents: Ideal for complex workflows needing custom logic, flexible prompt crafting, or specific LLM models. You control the entire interaction.
How it works 🏗️
End users interact with skillset-based extensions just like any other Copilot Extension. Just type @ followed by the extension name and ask in natural language. Behind the scenes, Copilot:
- Analyzes the query to determine which skill to call
- Structures the API request based on your JSON schema
- Calls your endpoint to get the data
- Formats and generates the response in chat
Architecture

Requirements for extension builders
- Access to GitHub Copilot
- For organizational builds: Free, Team, or supported Enterprise Cloud organization types
- Skillsets only apply to extensions built as GitHub Apps, and not VS Code chat participants
Getting started 🚀
Check out our documentation to learn how to build your first skillset.
Already built a Copilot Extension as an agent? Existing agent extensions can be converted into skillsets, but one extension cannot be both a skillset and an agent.
We want to hear your feedback!
- Join the GitHub Community Discussion for high level questions
- For detailed feedback, feature requests and bug reports to Github (or any third-party publishers or client teams) please open an issue in the extensibility feedback repo