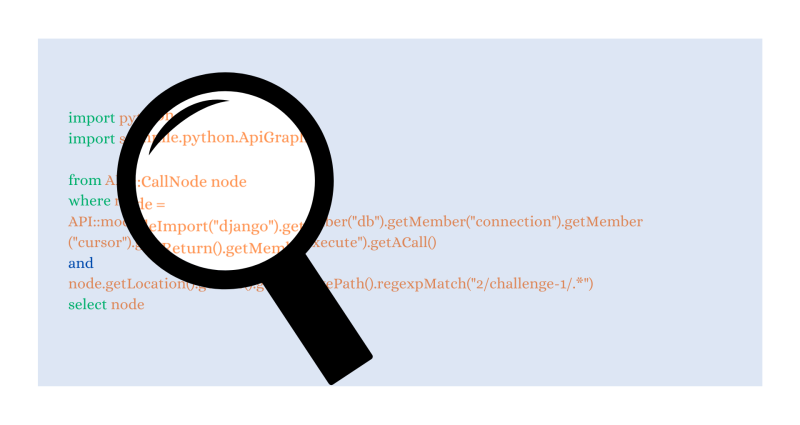
CodeQL zero to hero part 2: getting started with CodeQL
Learn the basics of CodeQL and how to use it for security research! In this blog, we will teach you how to leverage GitHub’s static analysis tool CodeQL to write custom CodeQL queries.
Category
Learn the basics of CodeQL and how to use it for security research! In this blog, we will teach you how to leverage GitHub’s static analysis tool CodeQL to write custom CodeQL queries.

GitHub’s VIP Bug Bounty Program has been updated to include a clear and accessible criteria for receiving an invitation to the program and more. Learn more about the program and how you can become a Hacktocat, and join our community of researchers who are contributing to GitHub’s security with fun perks and access to staff and beta features!

We’ve launched the beta of code scanning support for Swift. This launch, paired with our launch of Kotlin support in November, means that CodeQL covers both IOS and Android development languages, bringing a heightened level of security to the mobile application development process.

In this blog, I’ll look at CVE-2022-46395, a variant of CVE-2022-36449 (Project Zero issue 2327), and use it to gain arbitrary kernel code execution and root privileges from the untrusted app domain on an Android phone that uses the Arm Mali GPU. I’ll also explain how root cause analysis of CVE-2022-36449 led to the discovery of CVE-2022-46395.

GitHub Advanced Security for Azure DevOps is now available for public preview, making GitHub’s same application security testing tools natively available on Azure Repos.
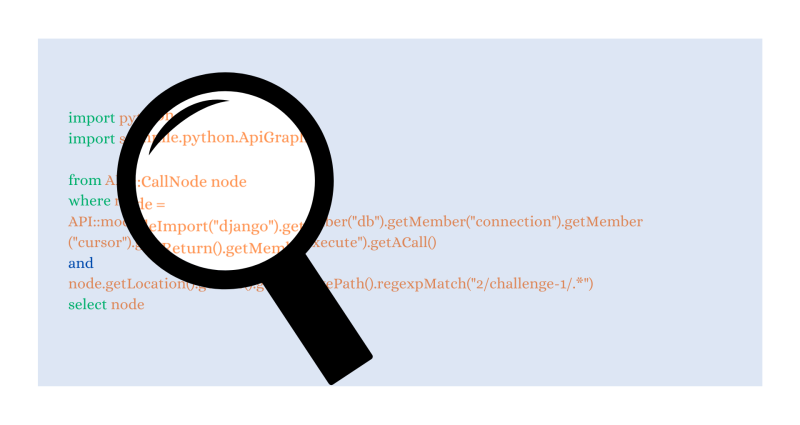
Code scanning detects ReDoS vulnerabilities automatically, but fixing them isn’t always easy. This blog post describes a 4-step strategy for fixing ReDoS bugs.

Announcing the general availability of push protection–a feature that proactively prevents secret leaks in your public and private repositories.

Code scanning’s tool status gives you a bird's eye view of your application security stack, allowing you to quickly confirm everything is working, or troubleshoot any tool in your application security arsenal.

A new alert rules engine for Dependabot leverages alert metadata to identify and auto-dismiss up to 15% of alerts as false positives.
A new set of Git releases were published to address a variety of security vulnerabilities. All users are encouraged to upgrade. Take a look at GitHub’s view of the latest round of releases.

Open source maintainers and security researchers embrace a new best practice to report and fix vulnerabilities.

How to verifiably link npm packages to their source repository and build instructions.

We’ve gotten great feedback on default setup, a simple way to set up code scanning on your repository. Now, you have the ability to use default setup across your organization's repositories, in just one click.
Explore how generative AI may soon help enable optimizing some of the foundational components of compliance.

In this post, I’ll look at a security-related change in version r40p0 of the Arm Mali driver that was AWOL in the January update of the Pixel bulletin, where other patches from r40p0 was applied, and how these two lines of changes can be exploited to gain arbitrary kernel code execution and root from a malicious app. This highlights how treacherous it can be when backporting security changes.