
Insider newsletter digest: How to use GitHub Copilot
Explore the July edition, featuring prompts, tips, and use cases for GitHub Copilot.
Category

Explore the July edition, featuring prompts, tips, and use cases for GitHub Copilot.
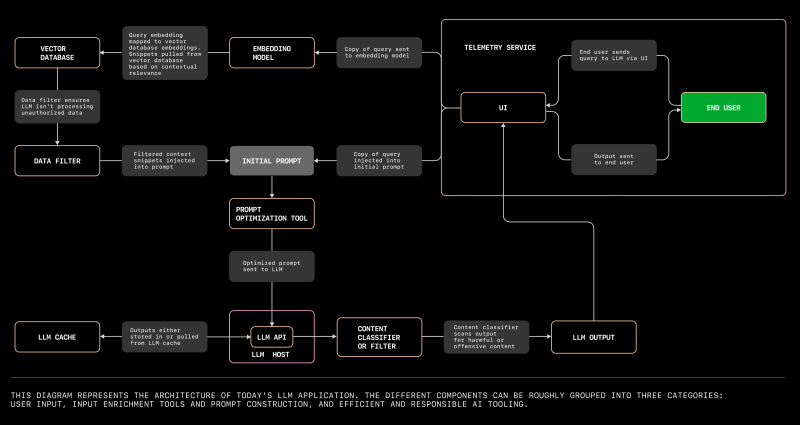
Here’s everything you need to know to build your first LLM app and problem spaces you can start exploring today.

Explore how LLMs generate text, why they sometimes hallucinate information, and the ethical implications surrounding their incredible capabilities.

Findings show that code quality is better across the board and developers felt more confident, too.
Speed up your GitHub Actions jobs on macOS with all new, faster Apple silicon powered M1 macOS larger runner for arm64.
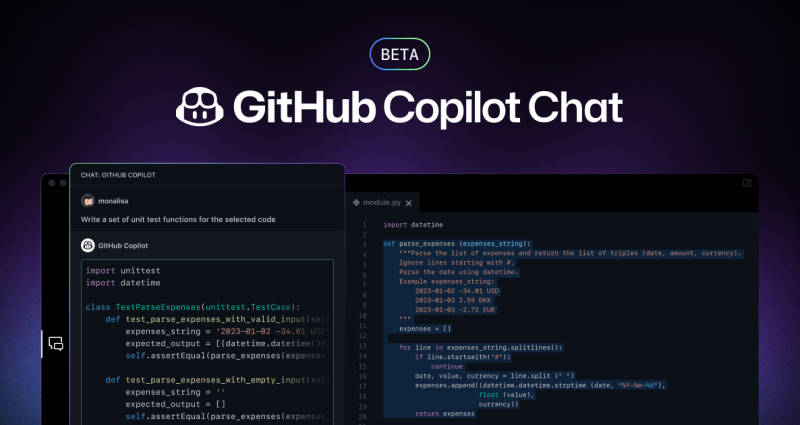
All GitHub Copilot for Individuals users now have access to GitHub Copilot Chat beta, bringing natural language-powered coding to every developer in all languages.

Customers using GHES can now ensure secure development is a top priority with enhanced security and compliance controls for their repositories.
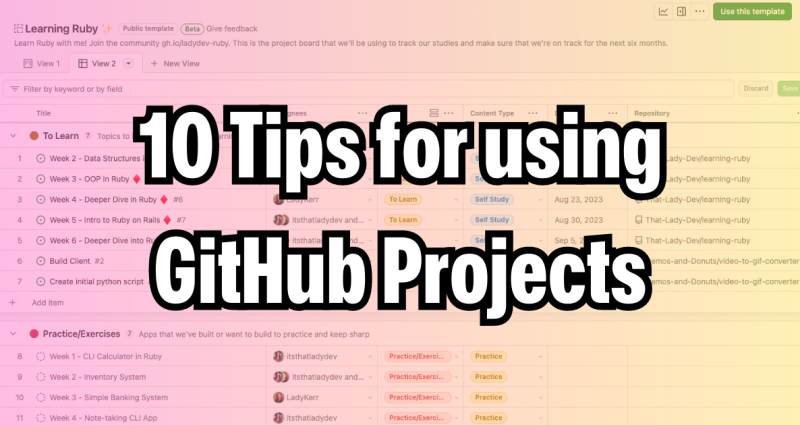
Learn how to optimize your usage of GitHub Projects to plan and track your work from idea to production.

Now, you can group multiple version updates in a single pull request.
GitHub’s design experts share 10 tips and lessons for designing magical user experiences for AI applications and AI coding tools.

In the world of software development, collaboration can make the difference between a brittle last-minute release and a reliable, maintainable, pain-free project. Whether you’ve been coding for a day or a decade, your colleagues are there to help strengthen your work. But they can only help if you’ve given them the tools to do so.
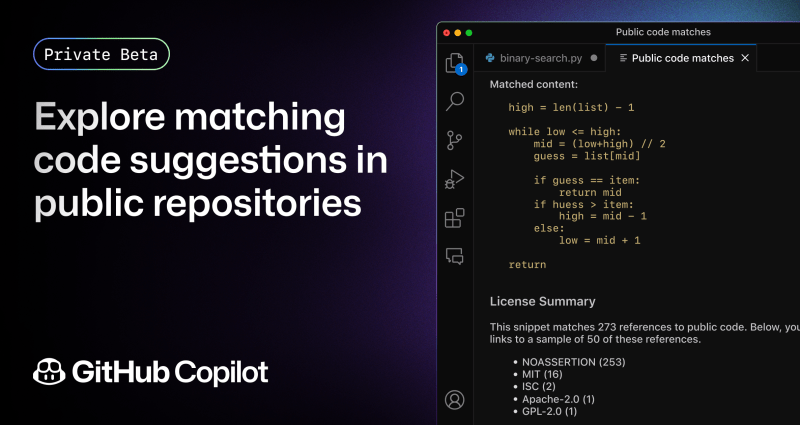
Today, we’re announcing a private beta of GitHub Copilot with code referencing that includes a filter to detect code suggestions matching public code on GitHub.

We're thrilled to announce two major updates to GitHub Copilot code Completion's capabilities that will help developers work even more efficiently and effectively.
We’re launching the GitHub Copilot Trust Center to provide transparency about how GitHub Copilot works and help organizations innovate responsibly with generative AI.