From macOS runners to secure deployments, what’s new from GitHub Actions
Read a roundup of the exciting, new innovation coming from GitHub Actions.

GitHub Actions is not just your average CI/CD and automation tool. Integrated natively in the GitHub Enterprise platform, Actions adds the “flow” into developer workflow. Designed with developers in mind, GitHub Actions balances the extensibility and flexibility required to quickly and easily build CI/CD workflows, while also offering key governance and security features and compute in a range of sizes that scale with you as you grow. Simply put, GitHub Actions lets teams automate away the repetitive tasks and bottlenecks that slows them down so developers can focus on coding.
Let’s take a look at the most recents Actions releases that were built to help you build simple, secure, scalable CI/CD and automation workflows in GitHub.
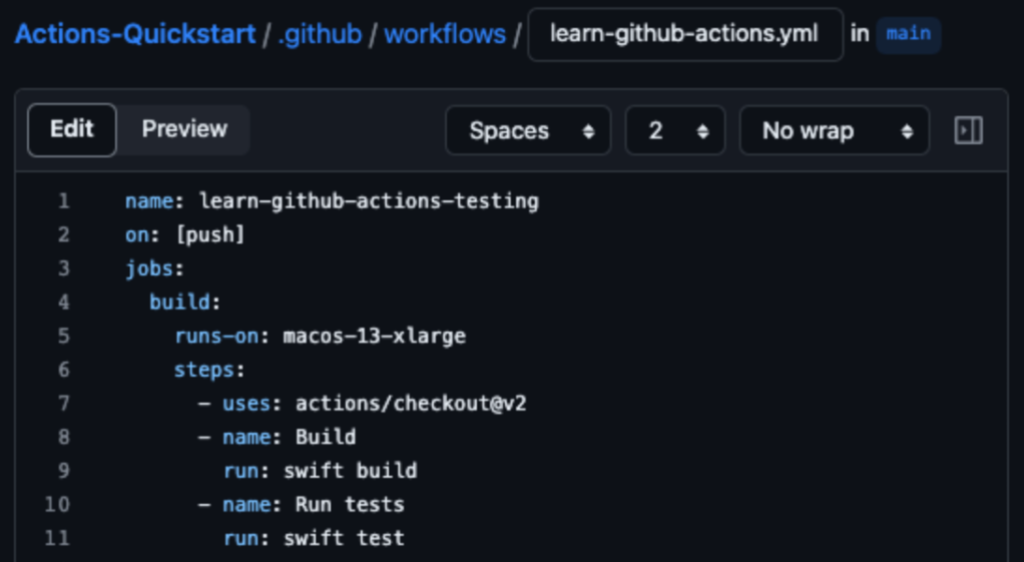
Apple silicon powered M1 macOS runners
Over the last few years, GitHub Actions has continued to evolve into a mature CI/CD platform. Today, it’s more powerful than ever with the addition of M1 macOS runners. The M1 macOS runner comes with GPU hardware acceleration enabled by default. Workloads are transferred from the CPU to the GPU for improved performance and efficiency. The runner is equipped with a 6-core CPU, 8-core GPU, 14 GB of RAM, and 14 GB of storage. It can reduce build times by up to 80% compared to the existing 3-core Intel standard runner, and up to 43% compared to the existing 12-core Intel runner. GitHub’s larger runners ensure that no matter how enormous your codebase is, you can build, test, and deploy it in a matter of minutes. To learn more about this release, check out this blog.
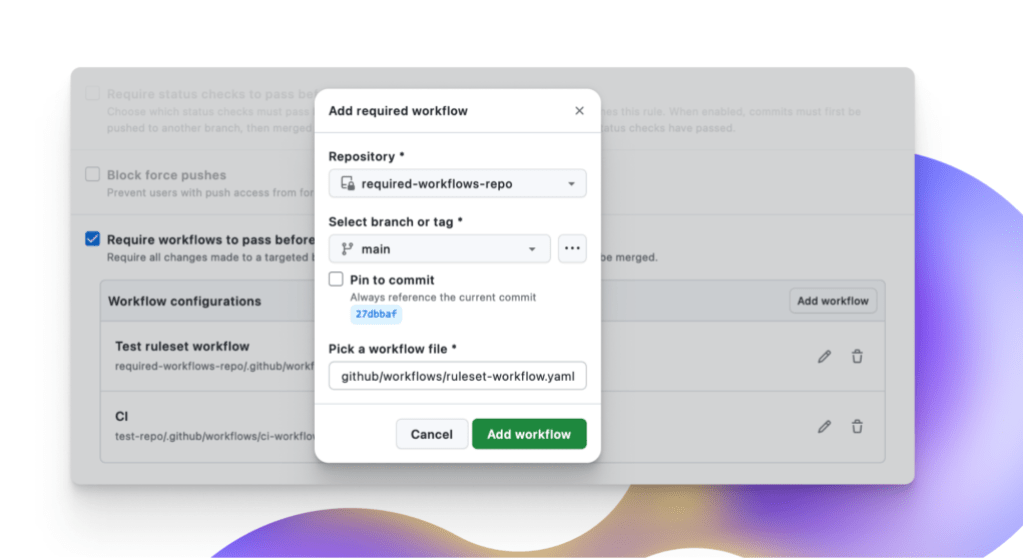
Requiring workflows with repository rulesets
Defining, setting up, and enforcing policy at scale—especially scaling to hundreds of repositories and thousands of developers–can be challenging. In order to help solve some of those difficulties GitHub has simplified the process of centrally managing workflows. With this feature GitHub Enterprise Cloud customers can require that certain workflows need to run successfully before code can be merged into an organization’s repositories. Now, code contributions are guaranteed to adhere to the CI/CD policies defined by required workflows. Not only do repository rulesets improve the experience of setting up and managing these workflows, it also allows several other benefits like branch targeting, bypass rules, and dry running rules in evaluation mode. To learn more about this release, check out this blog.
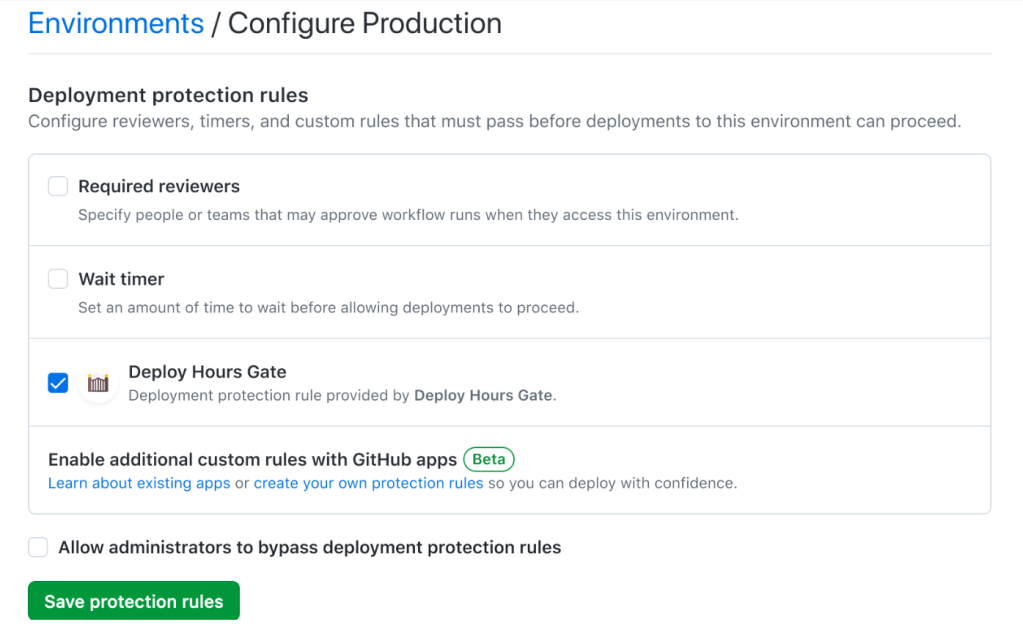
Keep your deployments secure with new continuous deployment features
The GitHub Actions team has been shipping lots of great features to help secure your deployments so you can ship with confidence.
- Custom deployment protection rules are powered by GitHub Apps and can be enabled on any GitHub org/repository/environment to allow external systems to approve or reject deployments. Each rule evaluates specific conditions in those external systems to assess the readiness of the environments for automated deployments, making them safer and more robust.
- New dashboard views for deployments across environments make it easy for developers and DevOps managers to view and track the full history of deployments in a repository or filter them across environments. Now, they can do things like view active deployments across various environments, monitor the deployment status, trace any deployment to its source workflow, and view logs to diagnose any issues, and more.
- We’ve also made it possible to control deployments for selected tag patterns. This capability makes it easy to specify selected tags or tag patterns on your protected environments in order to have more secure and controlled deployments.
- Now, admins can set controls to prevent self-reviews to ensure secure deployments across their GitHub Actions environments.
More secure GitHub-hosted runners
As customers increasingly migrate to using GitHub-hosted runners for their CI/CD scenarios, network security has become a top priority, specifically the ability to securely access private resources, control outbound access, and monitor network traffic as software is deployed. To address these needs, GitHub has introduced private networking with Azure Virtual Networks (VNET), now available in public beta for the GitHub Enterprise Cloud plan.
With this functionality, GitHub customers using Azure can now connect their GitHub Enterprise to an Azure VNET, owned and managed by their Azure account for GitHub-hosted runners to be deployed into. This allows customers to continue enjoying the benefits of GitHub-managed resources, but gives them full control over the networking policies of those resources. Once the runner is connected to the customer-owned Azure VNET, GitHub Actions workflows can securely connect to Azure services, such as Azure Storage, or to on-premises data sources, such as an artifactory, using existing pre-configured connections such as VPN gateway(s) and/or ExpressRoute(s). Additionally, any new or existing networking policies that are applied to the customer-owned VNet, such as network security group (NSG) rules to monitor and control inbound/outbound traffic, firewall policies etc. will also apply to the runners thus providing platform administrators full control on the network security of their build infrastructure.
Learn more about private networking with Azure VNET or sign up for the public beta waitlist.
Learn how industry experts accelerate development with GitHub Actions
We want you to get the most out of GitHub Action’s powerful automation and CI/CD features. So, we made sure to provide you with free learning paths rooted in real life customer stories to help you get up and running with GitHub Actions. Check out GitHub Learning Pathways for prescriptive modules that build foundational knowledge, proficiency, and expertise through guided tutorials, customer insights, and best practices from engineering leaders to learn how you can use GitHub Actions to help automate away the repetition and bottlenecks, so you can focus on innovation.
Tags:
Written by
Related posts

GitHub Universe is back: All together now, in the agentic era
GitHub Universe is back: returning to the historic Fort Mason Center in San Francisco on October 28–29, 2026.

GitHub Copilot app: The agent-native desktop experience
At Microsoft Build 2026, GitHub introduced new tools, updates, and surfaces so agents can work the way you already work.

Still a developer. Just outside. Our latest GitHub Shop collection is here.
The ESC collection lets you escape the confines of your desk and get out into the sun where good ideas are bound to happen.