Download GitHub Enterprise Server 3.11 now. For help upgrading, use the Upgrade Assistant to find the upgrade path from your current version of GHES to this new version.
GitHub Enterprise Server 3.11 is now generally available
Customers using GitHub Enterprise Server can gain more insight and understanding into the security of their code.

GitHub Enterprise Server 3.11 is now generally available. With this version, customers have access to tools and features that provide a better understanding and visibility into the security of their code.
Highlights of this version include:
- Scale your application security testing with code scanning’s default setup, which now helps you to schedule weekly scans and deploy across your organization in just a few clicks (#759, #784)
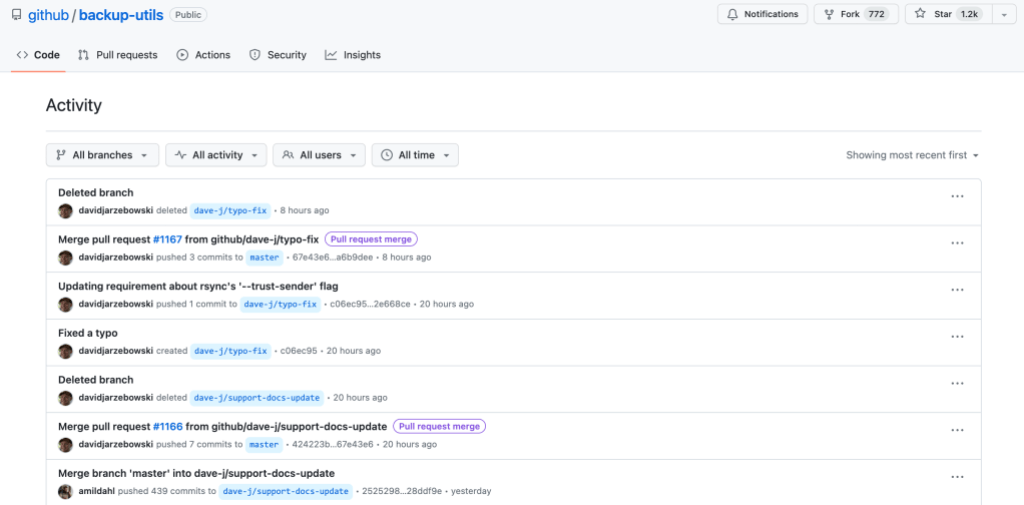
- The new Activity view makes viewing repository history much easier by showing activities like pushes, merges, force pushes, tag changes, and branch changes.
- Prevent secret leaks with data-driven insights and new metrics on secret leak prevention in security overview (#603)
- A GitHub CLI extension for the Manage GitHub Enterprise Server API to interact with your GitHub Enterprise Server instance via the
ghcommand-line interface. (#817)
Understand and enforce rules around repository changes
The repository Activity view is now generally available and makes it simple to see what changes have been made, and by whom. For example, you can use this view to find a force push on a particular branch, and then compare the state of the repository before and after the push.
Repository rules provide an easy, flexible way to define branch protections and ensure consistency in code across repositories. Rules can be enforced across all or a subset of repositories in an organization. No more tedious audits checking to see if a rule existed; now, you can ensure consistency in one location. You can trial them in evaluate mode if you’re not ready to commit to a rule. Rule insights allow you to see what would happen for your evaluated rules or what did happen for active rules.
Scale your security program with automation, new detection and data-driven insights
Automate application security testing
Default setup for code scanning makes it easy to deploy static analysis testing across your codebase in just a few clicks. With this release, you can now take this automation further with automated weekly scanning. Automated weekly scanning enables you to stay secure by helping you prevent, detect, and fix vulnerabilities at scale.
And if you haven’t already used default setup, you can rely on new features like configuration support, which helps you automatically use the best configuration for your repository when languages change and enablement at the repository level, which lets you enable all eligible repositories in your organization in just a few clicks.
Prevent secret leaks with data-driven insights
With secret scanning push protection metrics, organizations can see the number of total secrets intercepted and the number of successfully blocked or bypassed secrets. Now, these metrics will also include insights like the most commonly blocked, alert saturation by repository, bypass trends, and more.
Expand your secret leak detection surface
Secret scanning users will now receive alerts for secrets detected in GitHub Issues, including in the title, body, and comments. This expanded coverage will also detect and surface secrets matching any custom pattern defined at the repository, organization, or enterprise levels.
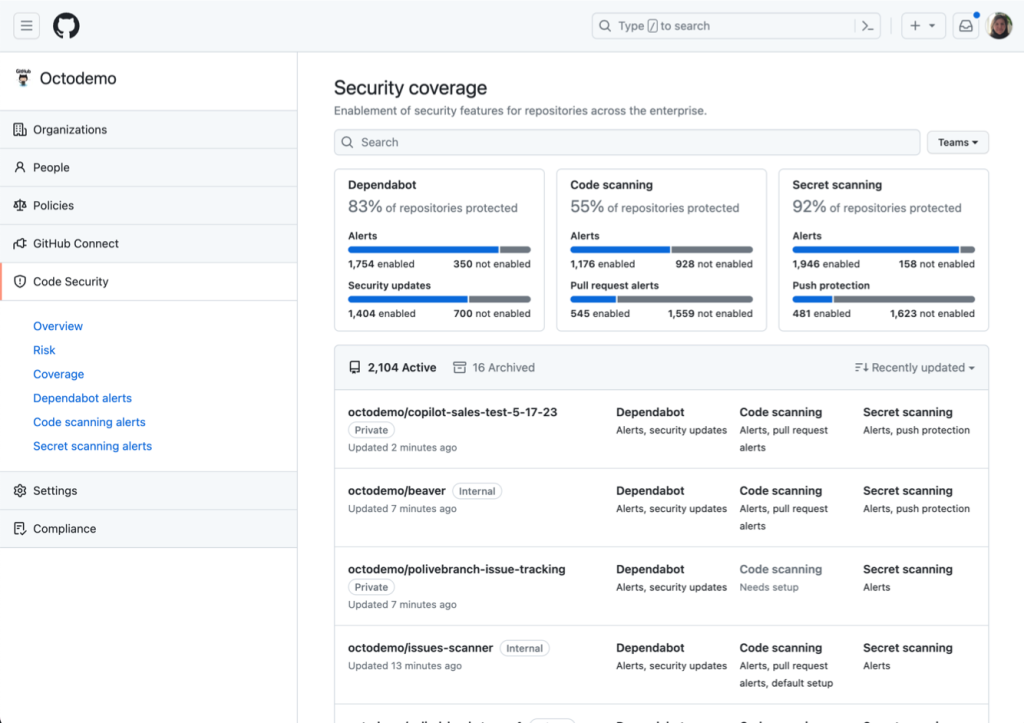
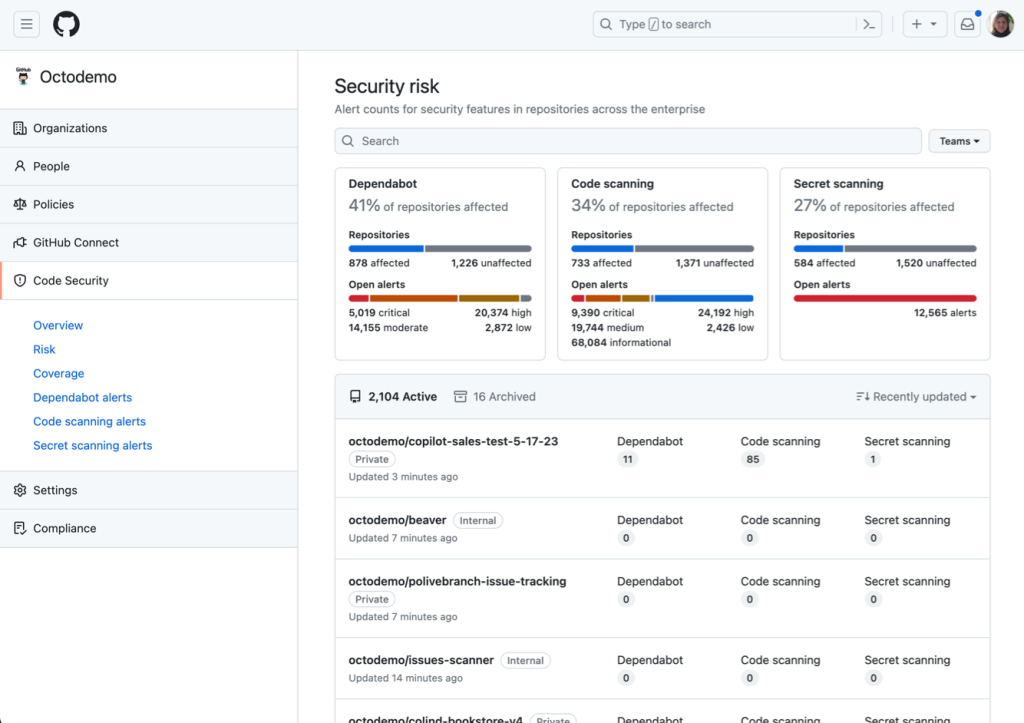
Better understand your holistic security posture with new analytics
Developers across the world use GitHub’s security products including Dependabot, code scanning, and secret scanning. But for security teams, we know that keeping an eye on all this action across your organizations can be tricky, which is why we built security overview–to give security teams a single pane of glass experience for viewing the risk and coverage of their security products. With security overview, GitHub’s native AppSec reporting view, you can uncover insights to help prioritize efforts in your AppSec program, and share progress with the various stakeholders across your organization.
We’ve added new views to the security overview to help you better understand your risk and coverage. The coverage view allows you to gain visibility into the enablement status of security features across all repositories within your enterprise and filter based on team, repository, testing type, and more.
Complementing the coverage view, the new risk view provides a comprehensive overview of all alerts across your enterprise. With the risk view, you can view the counts and percentages of repositories with security vulnerabilities and filter down based on severity, repository, and more.
Access more information with our REST API
Three new additions allow developers and administrators on GitHub Enterprise Server to access more information via our REST API. First, global security advisories from the GitHub Advisory Database can now be retrieved via our REST API. This allows developers to integrate real-time security vulnerability data into their workflows and applications.
Second, we have added a new header, x-accepted-github-permissions, which will be sent back to API callers that are using the fine-grained permission model (GitHub Apps and fine-grained personal access tokens). This header helps developers discover which permissions they need to call an API route, by returning the list of permissions you need to call a specific endpoint.
And third, a new extension to the GitHub CLI, gh-es, gives command line access to the endpoints available in the Manage GitHub Enterprise Server API. This allows administrators to quickly learn about their instances directly from the command line, without having to connect directly to an instance.
Try it out today
To learn more about GitHub Enterprise Server 3.11, read the release notes or download it now.
Not using GHES already? Start a free trial to innovate faster with the developer experience platform companies know and love.
Tags:
Written by
Related posts

Take your local GitHub sessions anywhere
Kick off work in VS Code or the CLI, finish it from your phone. Remote control for GitHub Copilot sessions is now generally available on github.com and GitHub Mobile.

GitHub availability report: April 2026
In April, we experienced 10 incidents that resulted in degraded performance across GitHub services.

GitHub Copilot individual plans: Introducing flex allotments in Pro and Pro+, and a new Max plan
Starting June 1, our lineup of individual plans will update based on your feedback.