Announcing general availability of GitHub Advanced Security for Azure DevOps
GitHub Advanced Security for Azure DevOps is now generally available. Enable secret scanning, dependency scanning, and code scanning on your organization directly in Azure DevOps configuration settings.

We live in a world fully consumed by software. According to the IDC, around 750 million applications will be shipped globally by 2025, meaning the feat of securing the world’s software is growing at an unprecedented rate at a time when digital trust has never been more important. At GitHub, we’re committed to empowering developers to not only create software, but ship secure products. GitHub Advanced Security (GHAS) was built to minimize context switching, reduce tooling, and allow you to rapidly find and fix vulnerabilities at the speed of innovation. Our application security testing solutions are natively embedded in the developer workflow and empowers DevSecOps teams to prioritize innovation and enhance developer productivity without sacrificing security.
But what does this look like in practice? Code scanning, our native SAST solution, surfaces the right alerts at the right time. When a security alert is triggered, it’s shown incrementally in the pull request. This is different from more traditional SAST tools, which may provide a long list of alerts to sort through when a scan is complete, lacking specific context. With this approach, users engage with almost 80% engagement of alerts surfaced by code scanning, leading to a 50% real-time fix rate in. This is 3.8X more effective than third-party alerts, where the engagement rate is around 16% and the fix rate is around 13%.
Today, with the general availability of GitHub Advanced Security for Azure DevOps, we are bringing GHAS’s native security features to the Azure DevOps workflow, meaning Azure DevOps users can benefit from the same advantages seen by GitHub Enterprise users. To get started today, any Azure DevOps Project Collection Administrator (PCA) can enable GitHub Advanced Security protections through the Azure DevOps configuration settings.
Rapidly deploy and scale your security program
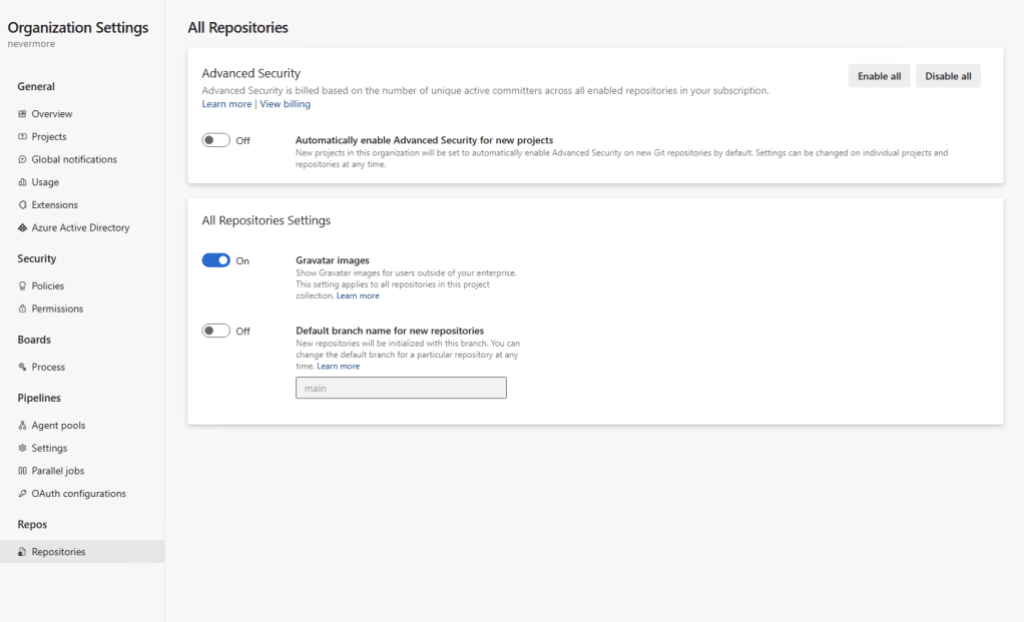
With general availability, we’ve added new functionality to help you quickly enable GitHub Advanced Security to cover your organizations repositories. You can now choose to enable GHAS at the organization or project level, as well as on individual repositories. This should allow you to quickly deploy GHAS, when you want it, where you want it.
When you enable GitHub Advanced Security for Azure DevOps, you’ll receive a prompt that will alert you that this is a billable event and give you an estimate of the number of committers.
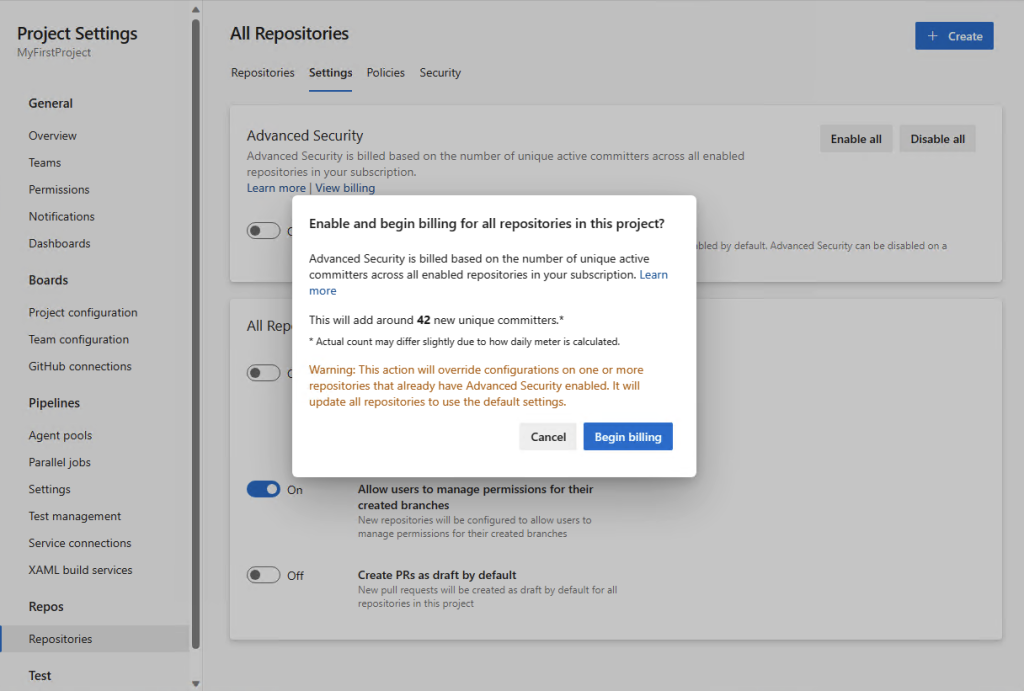
You can also now choose for Advanced Security to be automatically enabled for any future repositories you and your teams create.
View all your alerts in a single pane of glass
A key part of any successful application security program is a way to view all your alerts, across your organization, in a single pane of glass. This ensures you and your team have maximum visibility into your application security posture. We’ve taken this necessary feature, and built on it with our partnership with Microsoft Defender for Cloud (MDC). You can now not only view all Advanced Security alerts across your Azure repositories within MDC, but can also view alerts from GitHub as well. This functionality is available in the free tier of MDC, ensuring any team can take advantage of this powerful integration.
Getting started with GitHub Advanced Security for Azure DevOps
If you’re interested in getting started with GitHub Advanced Security for Azure DevOps, please see our documentation.
Need more information? We will also be hosting a webinar on October 4, 2023, at 11 am PT. There, you can learn more about the importance of application security, our unique approach, and see a demo of GitHub Advanced Security for Azure DevOps in action.
Tags:
Written by
Related posts

GitHub Universe is back: All together now, in the agentic era
GitHub Universe is back: returning to the historic Fort Mason Center in San Francisco on October 28–29, 2026.

GitHub Copilot app: The agent-native desktop experience
At Microsoft Build 2026, GitHub introduced new tools, updates, and surfaces so agents can work the way you already work.

Still a developer. Just outside. Our latest GitHub Shop collection is here.
The ESC collection lets you escape the confines of your desk and get out into the sun where good ideas are bound to happen.