Ensuring compliance in developer workflows
How GitHub Enterprise ensures secure and compliant developer workflows for highly regulated industries.

We recently walked through practical ways that you can start meeting compliance requirements without having to transform the culture in your company—all while enabling developers to stay in the flow. In this post, we focus on ensuring systemic compliance with regulatory frameworks without encumbering the developer experience and how GitHub Enterprise serves as the secure operating platform.
Software developers play a critical role in ensuring the security of an organization’s software development lifecycle, particularly in today’s ever-changing cybersecurity landscape. As such, many organizations must ensure that their software development practices comply with regulatory frameworks such as GLBA, SOX, and HIPPA. Developers should be equipped with the necessary tools and knowledge to maintain a secure operating environment that adheres to best practices. Fortunately, there are powerful resources available, including tools on the GitHub Enterprise platform, that can help organizations support developers and maintain a secure software development lifecycle.
Testing and validation
Application security tools are uniquely capable at pattern detection, and are responsible for driving remediation of common vulnerability patterns. GitHub code and secret scanning are features that empower you to automatically scan your code for vulnerabilities, security issues, and secrets from a large variety of service providers. Although an uncommon use case, these capabilities can be combined to reduce the probability that personally identifiable information (PII), personal health information (PHI), and payment card industry (PCI) data will be introduced unknowingly into your codebase by automatically scanning code on push or pull request. Secret scanning empowers AppSec engineers and developers to define custom patterns for detecting payment, user, or other sensitive data with “Hyperscan,” a more performant flavor of Regex. Administrators can enable push protection on secrets and custom patterns to prevent the data from making its way from the developer machine to your remote repository. Here is a useful set of predefined custom patterns for your consideration. For additional assistance, consider using GitHub Copilot to develop additional patterns.
With GitHub code scanning, out of the box, we provide queries such as ExposureOfPrivateInformation.ql for inclusion in your automated code scans to identify PII in a pull request. Specific queries can be included in your code scans as follows:
Queries:
- uses: ./my-queries/ExposureOfPrivateInformation.ql
Segregation of duties
Performing peer-led code reviews can help you ensure that your code is secure and introduces another layer of accountability for developers who are responsible for ensuring quality standards are being met. You can require approving reviews from people with write permissions in the repository or from a designated code owner. In Financial Services, Healthcare and other highly regulated industries, required reviews are a standard practice. Automated Code Reviews is also a common supplemental practice — these automation tools can provide an auditable signal as to whether a code change meets organizational requirements.
- Tech/Scrum leads or PMs can leverage Labeler or Stale issues to increase bandwidth and time by automating ticket triaging, project board ops, and synchronizing developer focus with business outcomes.
-
Build and QA engineers can leverage tools like Ponicode to automatically generate unit tests as changes are made to the repository to reduce technical debt, while CodeCov uploads the results back in a centralized dashboard.
Change management
GitHub Actions can be interspersed within every step of your Software Development Lifecycle (SDLC) to ensure standardization and compliance at scale. Leveraging required workflows ensures every developer automatically has the scaffolding in place for security while standardization is achieved – via readily available workflow templates and reusable workflows which make it easy to share “gold standard” pipelines across your organization.
Rather than storing your credentials and sensitive data externally, developers should leverage OIDC or GitHub Secrets, which are encrypted variables that you create in an organization, repository, or repository environment. Repository environment secrets allow different encrypted variables to be called on within the environment they are chosen for; consider these environments (dev, qa, prod) as examples. It is a recommended security practice that each environment would have its own secrets and be accessible only to the teams that have permissions within that environment. The secrets that you create are available to use in GitHub Actions workflows without ever showing up in your runtime logs.
Access controls and monitoring
Operating securely within the platform provides administrators a thoughtful approach to enterprise configurations. For example, GitHub provides detailed logging and monitoring capabilities that can help you track changes across your enterprise and identify potential security concerns in real time. This can include the ability to see who had access and made changes to your code, when those change were made, and what the changes were. In addition to repository level auditing and logging, GitHub Enterprise provides auditability at the organization and enterprise account levels. Consider automatically streaming audit logs to one of the supported providers and enabling anomaly detection downstream for identifying potentially malicious activity.
As a standard, GitHub supports the encryption of sensitive data both in transit and at rest. This ensures that data is protected from unauthorized access or interception. Sensitive client data should be protected by encryption when possible, passing through internal services. As previously stated, push protections are a preventative measure to ensure that along with a large variety of service provider tokens, PII, PHI, and payment data is never committed back to your repository.
At GitHub, we use GitHub to manage and distribute our compliance documentation. Distribution is particularly important for our highly regulated customers who use GitHub at scale and seek to demonstrate due diligence when adopting and maintaining the platform. For InfoSec certification you can access GitHub’s compliance reports, such as our SOC reports and Cloud Security Alliance CAIQ self-assessment (CSA CAIQ), or view our ISO/IEC 27001:2023 certification and our Services Continuity and Incident Management Plan.
Enterprise engineering leaders can enhance their development workflows by leveraging GitHub Enterprise and relying on the platform’s built-in capabilities to ensure operational compliance. Incrementally adopting these features, such as push protections and required reviews; can improve code quality and security without compromising productivity. By layering these enhancements with adherence to industry frameworks, organizations can streamline their development processes and stay ahead in today’s fast-paced business landscape. GitHub provides training and education resources to help developers understand how to write secure code and understand their regulatory requirements.
While GitHub Actions, GitHub Apps, and GHAS can be powerful tools for implementing layers of controls for security and compliance to reduce risk, it does not replace a comprehensive compliance program. Teams should consult with their compliance department and legal counsel to ensure that they are implementing the appropriate controls and using the right tools and capabilities provided by GitHub.
Next steps
Thank you for joining us as we covered areas of compliance and security within the developer experience. We covered secret scanning, custom patterns, and push protections to prevent the exposure of sensitive information, including valid secrets and tokens. We also covered the need for peer code reviews and we discussed standardization with Actions required workflows, reusable workflows, and workflow templates to improve developer velocity.
GitHub continues to focus on providing tools and features that reduce developer friction. These tools reduce context switching and provide an educational experience enhanced by shift-left security, standardization, reusability, and traceability.
Tags:
Written by
Related posts

Improving token efficiency in GitHub Agentic Workflows
Agentic workflows that run on every pull request can quietly accumulate large API bills. Here’s how we instrumented our own production workflows, found the inefficiencies, and built agents to fix them.
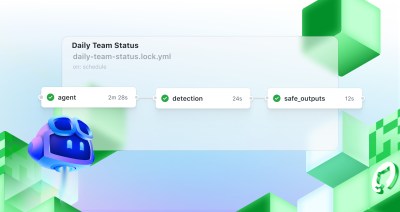
Automate repository tasks with GitHub Agentic Workflows
Discover GitHub Agentic Workflows, now in technical preview. Build automations using coding agents in GitHub Actions to handle triage, documentation, code quality, and more.

Level up design-to-code collaboration with GitHub’s open source Annotation Toolkit
Prevent accessibility issues before they reach production. The Annotation Toolkit brings clarity, compliance, and collaboration directly into your Figma workflow.