All GitHub Enterprise users now have access to the security overview
Today, we’re expanding access to the GitHub security overview! All GitHub Enterprise customers now have access to the security overview, not just those with GitHub Advanced Security. Additionally, all users within an enterprise can now access the security overview, not just admins and security managers.
GitHub’s security features empower developers to find and remediate application security risks across both public and private repositories. Until today, visibility into your security risk across your repositories was only available for admins and security managers for organizations with GitHub Advanced Security.
Today, we’re expanding access to GitHub’s security overview pages in two ways. Firstly, all GitHub Enterprise accounts now have access to the security overview, not just those with GitHub Advanced Security. Secondly, all users within an enterprise can now access the security overview, not just organization owners and security managers. The security overview each user sees is scoped to the repositories and alerts they have access to. Users with write access to repositories will see code scanning alert counts and enablement details for those repositories; users with admin access to repositories will see Dependabot and secret scanning alert counts and enablement details for those.
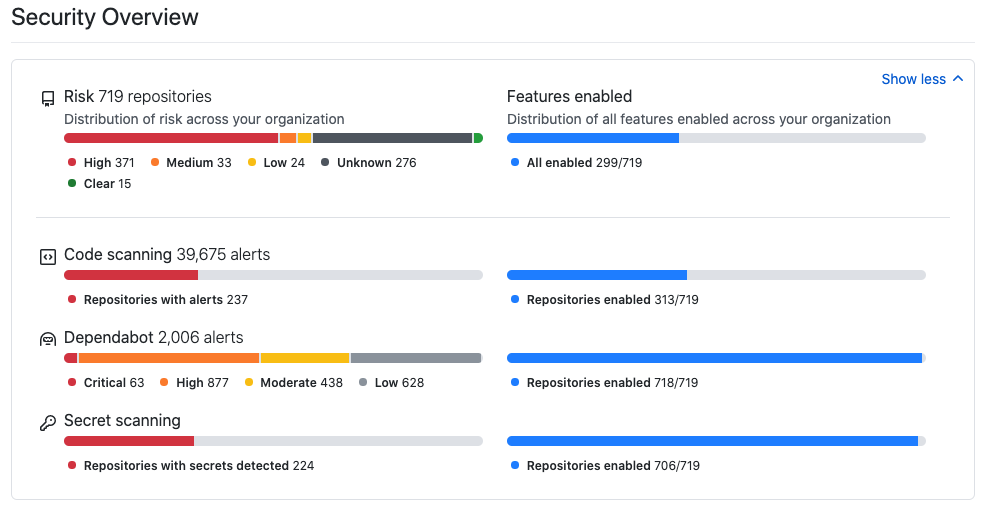
Security overview provides a centralized view of risk for application security teams, engineering leaders, and developers who work across hundreds—or even thousands—of repositories. In the security overview dashboards, you can see code scanning, Dependabot, and secret scanning alerts across every repository you have access to. The security overview also shows you where you have unknown risks because security features haven’t been enabled.
What kind of alerts can I expect to see in the security overview?
The security overview provides visibility into what security features you have enabled across all repositories in your organization. It surfaces information about any repositories for which you are an admin or security manager.
Dependabot alerts can be enabled on any repository. They provide details of any vulnerable dependencies being used across your organization based on the information in the GitHub Advisory Database.
Code scanning alerts can be enabled on any public repository or any private repository with GitHub Advanced Security. They surface potential vulnerabilities in your own code discovered by our industry-leading scanning engine, CodeQL, or a third-party static analysis tool that you’ve configured.
Secret scanning alerts can be enabled on any repository with GitHub Advanced Security. They surface credentials committed in your code, which could lead to unauthorized access to your infrastructure or third-party services. In addition, GitHub scans all pushes to public repositories for secrets, and sends findings to our secret scanning partners for them to help resolve. For example, if you commit an AWS key and secret to a public repository, you’ll get a message from AWS in seconds alerting you.
Learn more about security overview
The security overview provides a comprehensive set of filters so you can concentrate on just a subset of repositories. If you’re only interested in high-risk public repositories with Dependabot alerts, for example, you can limit your view to just those. You can conduct targeted searches for a particular kind of alert open, such as a specific CVE.
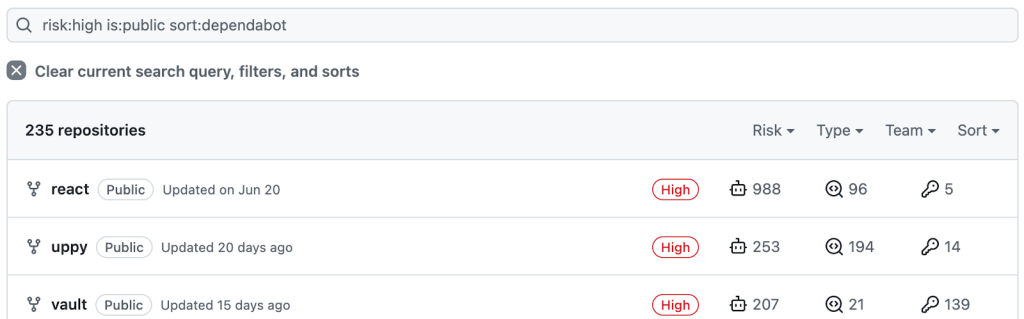
You can also get a bird’s-eye view of individual repositories—their assigned risk category, security features enabled, and active alert counts. From here, you can quickly drill into each repository to turn security features on or view the full list of alerts to take action.
Try GitHub Enterprise
To keep developers focused on learning and long-term growth, GitHub Enterprise simplifies your tech stack by providing tools for automation and security, all with an efficient interface that developers know and love! By reducing complexity, increasing transparency, and anchoring on a central platform, GitHub gives them the ability to focus on what you hired them to do. To learn more, trial GitHub Enterprise and see security overview in action.
Tags:
Written by
Related posts
GitHub recognized as a Leader in the Gartner® Magic Quadrant™ for Enterprise AI Coding Agents for the third year in a row
We are committed to empowering every developer by building an open, secure, and AI-powered platform that defines the future of software development.

Improving token efficiency in GitHub Agentic Workflows
Agentic workflows that run on every pull request can quietly accumulate large API bills. Here’s how we instrumented our own production workflows, found the inefficiencies, and built agents to fix them.
Automate repository tasks with GitHub Agentic Workflows
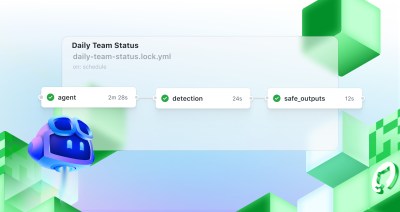
Discover GitHub Agentic Workflows, now in technical preview. Build automations using coding agents in GitHub Actions to handle triage, documentation, code quality, and more.