Get started with ease using security workflows!
GitHub Actions workflows in the Security category will now appear among the workflow recommendations based on a repository’s content.
A couple months ago, we announced improvements to the GitHub Actions “new workflow” experience, where we now recommend continuous integrations and deployment-related workflows based on an analysis of repository content.
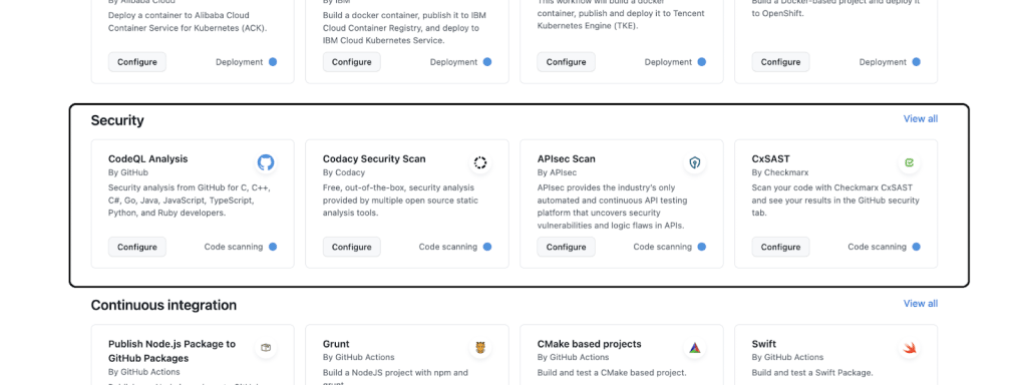
Today, we are adding a Security category alongside the three existing categories – Automation, Continuous Integration, and Deployment. In-line with the other categories, workflows in the Security category will be recommended based on a repository’s content. To start with, we are adding code scanning workflows to the Security category to help prevent vulnerabilities from reaching production. These workflows can be scheduled to scan on specific days and times, or can be triggered when a certain event occurs in the repository, such as a push, to identify any vulnerabilities in your code.
Also, this allows customers to discover and configure code scanning workflows from the central GitHub Actions “new workflow” experience, as opposed to earlier when they had to navigate to the Security tab to set these up.
Additionally, we go one step further under the Security category and guide you to enable GitHub Advanced Security wherever applicable to configure these workflows.
How to get started
- These capabilities are available for all GitHub.com and GitHub Enterprise Cloud organizations today.
- Under the “Actions” tab in your repository, select “New Workflow.” Use the Security category, search, and filtering capabilities to find relevant templates.
New to using GitHub Actions workflows?
You can learn more about GitHub Actions workflows in our documentation. For any questions or suggestions, join the discussion here.
Tags:
Written by
Related posts

Take your local GitHub sessions anywhere
Kick off work in VS Code or the CLI, finish it from your phone. Remote control for GitHub Copilot sessions is now generally available on github.com and GitHub Mobile.

GitHub availability report: April 2026
In April, we experienced 10 incidents that resulted in degraded performance across GitHub services.

GitHub Copilot individual plans: Introducing flex allotments in Pro and Pro+, and a new Max plan
Starting June 1, our lineup of individual plans will update based on your feedback.