Audit log streaming is now in public beta
If you’re a GitHub Enterprise Cloud customer, you can now set up a stream of audit log and Git events to Splunk or an Azure Event Hub.
If you work in an enterprise environment, audit and compliance considerations often factor heavily into system design. Starting today, if you’re a GitHub Enterprise Cloud customer, you can set up a stream of audit log and Git events to Splunk or an Azure Event Hub. The stream forwards every one of these events in near real time, and retains data for playback for up to seven days in case you need to pause data collection.
More tools for more jobs
We want enterprise administrators to be able to use the right tools for the job they need to do, whether that be short term investigation or longer term threat analysis and prevention. Earlier this year we released the audit log and Git events API to help with immediate short-term needs. With audit log streaming, no audit log event will be lost. You will be able to satisfy longer term data retention goals by storing streamed events within your own data collection systems. Analysis tools become more powerful as the dataset grows, making the Security Information and Event Management (SIEM) tool of your choosing the best place to parse GitHub audit log and Git events for months and years to come.
More value from your data
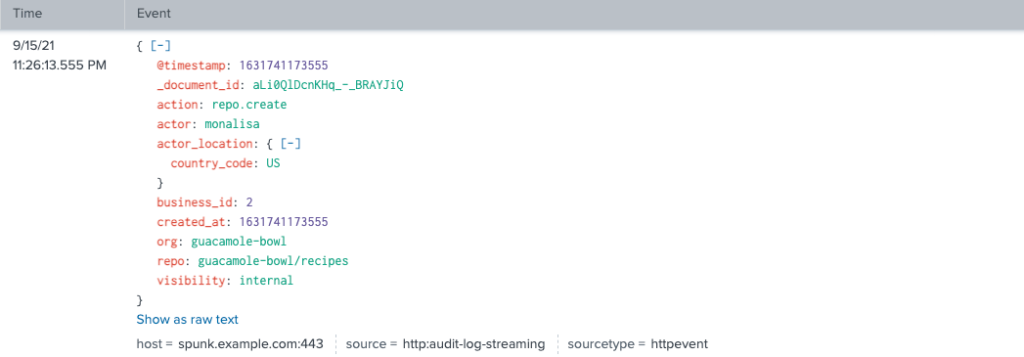
The majority of the events that will be generated by any enterprise will be Git events. The best ways to look at these events will be with our API and with the streaming capability, but the API will only return Git events data for the previous seven days. With audit log streaming, GitHub Enterprise Cloud customers will have the opportunity to look for patterns in Git activity for as long as they choose to retain that data. As you can see from the following examples, the metadata within these events are the same for both the API and for the streaming payload. The only differences are data retention period and tool choice.
API repo create event

Streaming repo create event
Filtering events for a specific organization
A common pattern we expect to see will be users filtering on events related to a specific GitHub organization. In the audit log streaming feature, this will work just like you’ve come to expect from the UI and API where you can filter on org="organization-name" to get results specifically pertaining to organization-name. If you’re a Splunk user, this is how you would do that in the Splunk web client:
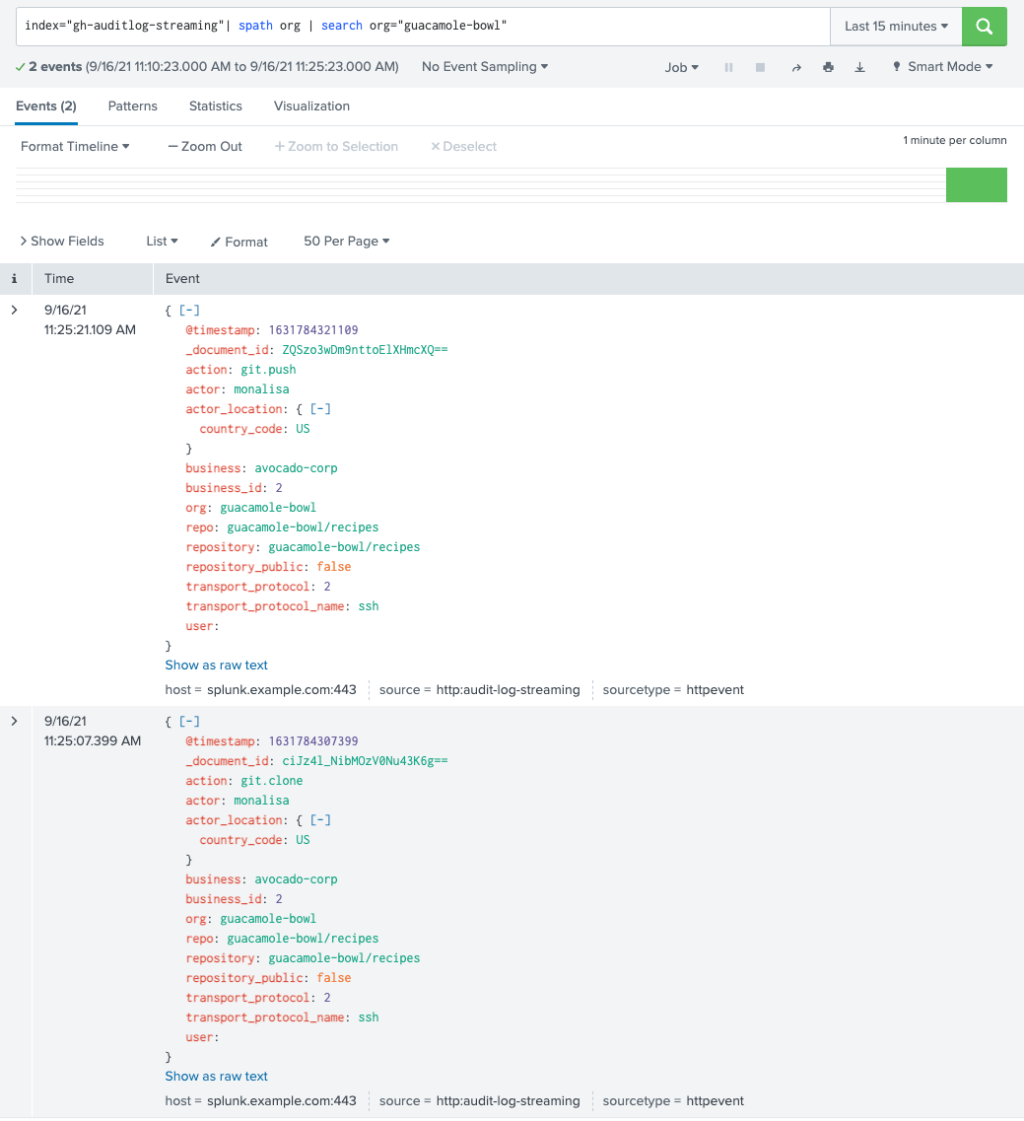
You can also use Splunk’s add-on for GitHub to see other use cases and dashboards.
Adding more integrations
While we are in public beta, we will expand the number of options you have for where you can stream your audit and Git events while also improving the administrative experience within GitHub. You may not know what analysis tools you want to use today, but that shouldn’t stop you from setting up a stream right away. If this sounds like your use case, we will be adding support for these popular cloud storage systems to make it easier to get started:
Additionally, we are looking to add support for more SIEM partners and deeper integrations with threat prevention tools like Azure Sentinel.
Supporting you and gathering your feedback
In order to understand the current state of your stream, we will be adding more status and error handling information, in addition to other user interface improvements as we add more supported integrations. If you run into any trouble or have questions, please contact support@github.com.
Get started with the beta today!
Set up your stream in minutes by following our documentation, navigating to your enterprise account settings under the audit log tab, and configuring your collection endpoint.
Keep an eye on the GitHub Changelog for beta updates and on the public roadmap for general availability.
Tags:
Written by
Related posts

GitHub Universe is back: All together now, in the agentic era
GitHub Universe is back: returning to the historic Fort Mason Center in San Francisco on October 28–29, 2026.

GitHub Copilot app: The agent-native desktop experience
At Microsoft Build 2026, GitHub introduced new tools, updates, and surfaces so agents can work the way you already work.

Still a developer. Just outside. Our latest GitHub Shop collection is here.
The ESC collection lets you escape the confines of your desk and get out into the sun where good ideas are bound to happen.