15+ new code scanning integrations with open source security tools
Today, we’re happy to announce more than 15 new integrations with open source security tools that broaden our language coverage to include PHP, Swift, Kotlin, Ruby, and more.
Last year, we released code scanning, a vulnerability detection feature in GitHub Advanced Security that’s also free on GitHub.com for public repositories. With code scanning, you can use GitHub CodeQL for static analysis, or you can choose from one of the many third-party integrations available in the GitHub Marketplace to execute security scans in your continuous integration pipeline and surface the results directly in GitHub. Today, we’re happy to announce more than 15 new integrations with open source security tools that broaden our language coverage to include PHP, Swift, Kotlin, Ruby, and more.
Below is a list of all the new integrations, with links to their GitHub Actions in the GitHub Marketplace. These integrations are brought to us by a number of key contributors from our open source community. Big thanks to @ajinabraham, @Moose0621, @GeekMasher, @Muglug, @GriffinMB, @jarlob, @presidentbeef, @A-Katopodis, @OwenRumney, @swinton and others for their contributions to the growing ecosystem of open source static analysis tools.
New open source scanner integrations
Mobile languages
Detekt is a static code analysis tool for the Kotlin programming language. A GitHub Action is available for Detekt, and a preconfigured workflow for Static Analysis Results Interchange Format (SARIF) upload is available in the GitHub user interface (UI) under the “Security” tab.
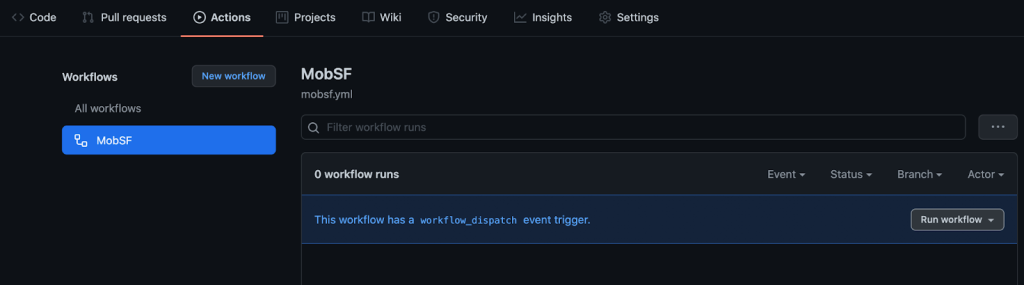
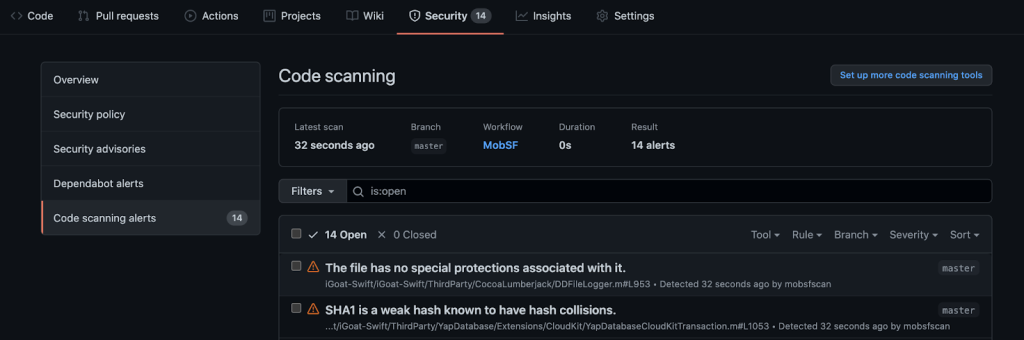
MobSF is an automated, all-in-one mobile application framework (Android/iOS Swift/Windows) for pen testing, malware analysis and security assessment that’s capable of performing static and dynamic analysis. With the help of @ajinabraham, MobSF now supports code scanning. Check out the GitHub Action or find it in the GitHub “Security” tab.
Big thanks to our own @Moose0621 and @GeekMasher for adding these popular tools for mobile applications! Kotlin and Swift support are forthcoming in CodeQL.
PHP
Psalm is an open source tool for finding security vulnerabilities in PHP supported by @Muglug and Vimeo. Try the Psalm GitHub Action with SARIF upload.
Elixir Phoenix Framework
Soblow is the security-focused static analyzer for the Elixir Phoenix Framework. @GriffinMB gave a helping hand by adding SARIF support and writing a GitHub Action.
Node JS
nodejsscan is a static security code scanner (SAST) for Node.js applications. @Ajinabraham added a GitHub Action and added it to the GitHub UI!
Node JS support is also available natively in CodeQL.
Electron
Electronegativity is a tool to identify misconfigurations and security anti-patterns in Electron-based applications. Check out the GitHub Action written by @jarlob.
Ruby on Rails
Brakeman is a static analysis tool which checks Ruby on Rails applications for security vulnerabilities. GitHub’s @swinton added support for SARIF, which can be configured in the available actions or from the GitHub UI starter workflow in your “Security” tab. Thanks @presidentbeef for the pull request review!
Ruby support is forthcoming in CodeQL, too.
Powershell
PSScriptAnalyzer is a static code checker for PowerShell modules and scripts. A GitHub Action was written by @A-Katopodis and it’s available in the GitHub UI.
Kubernetes YAML
Kubesec, backed by Control Plane, provides security risk analysis for Kubernetes resources and is now available in the GitHub UI or via their GitHub Action.
Terraform
tfsec uses static analysis of your terraform templates to spot potential security issues. Try the GitHub Action or find it in the Security UI. Thanks for the pull request, @OwenRumney!
C/C++
MSVC code analysis is the C/C++ correctness checker behind the Microsoft compiler.
Flawfinder is a C/C++ source code security checker and is available under the GitHub “Security” tab.
These languages are covered by CodeQL natively, but as the old adage goes: measure twice, cut once!
Multiple languages: Java, Go, Ruby, Python and more
Semgrep, sponsored by r2c, supports a variety of languages and added GitHub SARIF upload via workflow file, and is available in the GitHub UI.
Security Code Scan is a vulnerability patterns detector for C# and VB.NET and added a GitHub Action with help from @jarlob.
C# support is also available in CodeQL.
DevSkim supports C, C++, C#, Cobol, Go, Java, Javascript/Typescript, Python, and more.
Contribute to the code scanning ecosystem
If you contribute to a static analysis tool, linter, or container scanning tool, you can easily integrate your project with code scanning by following our step by step guide to list your project directly in the GitHub UI and surface your scan results under the GitHub “Security” tab.
Fuzzers and dynamic application security testing (DAST) tools can also follow a pattern of uploading their results, similar to ForAllSecure’s Mayhem for API action or the StackHawk HawkScan action, which adds a link to DAST output in the SARIF help text metadata field.
Give code scanning a try
If you haven’t tried code scanning, now’s a great time to explore this capability and its many integrations. From the “Security” tab in the GitHub UI, you can configure code scanning on any public repository using CodeQL, or you can try one of our pre-configured Octodemos for Android Kotlin, iOS Swift, JavaScript, Terraform, or PHP. Below is a quick example using MobSF for iOS Swift.
- To try code scanning with MobSF, navigate to: https://github.com/octodemo/advance-security-mobile-ios
- Fork the repository to your GitHub Account. (Note that this demo uses OWASP iGoat Swift – A Damn Vulnerable Swift Application for iOS, a deliberately vulnerable application for code scanning demonstration purposes only!)
- Click the Actions tab and enable actions if required. 1000 free minutes are included in your GitHub account.
- Click on the MobSF workflow, then click Run workflow and run the workflow manually.
- In about a minute, you’ll see results populate in the “Security” tab under “Code scanning alerts.”
With GitHub Advanced Security, configuring a static analysis tool and delivering the results in context on every pull request is that simple! If you’d like a hands on demo for your organization don’t hesitate to contact us.
Tags:
Written by
Related posts

GitHub Universe is back: All together now, in the agentic era
GitHub Universe is back: returning to the historic Fort Mason Center in San Francisco on October 28–29, 2026.

GitHub Copilot app: The agent-native desktop experience
At Microsoft Build 2026, GitHub introduced new tools, updates, and surfaces so agents can work the way you already work.

Still a developer. Just outside. Our latest GitHub Shop collection is here.
The ESC collection lets you escape the confines of your desk and get out into the sun where good ideas are bound to happen.