Keep your dependencies secure and up-to-date with GitHub and Dependabot
The following is a guest post written by Dependabot’s co-founder, @greystiel. Modern software often relies on hundreds of open source components, all of which need to be kept secure. Staying on top…

The following is a guest post written by Dependabot’s co-founder, @greystiel.
Modern software often relies on hundreds of open source components, all of which need to be kept secure. Staying on top of security vulnerabilities in those dependencies requires constant vigilance, and the results of neglecting them can be catastrophic. Dependabot taps into the GitHub Security Advisory API to automate the process and create pull requests to fix vulnerabilities as they’re found.
Applications rely on hundreds of open source dependencies
The average Ruby application using Dependabot pulls in over 100 dependencies, and the average JavaScript application has a whopping 742. The majority of those dependencies are “transitive,” meaning they’re pulled in by other dependencies without a direct link between them and the application using them.
| Direct dependencies | Indirect dependencies | Total | |
| JavaScript | 30 | 712 | 742 |
| Ruby | 38 | 87 | 125 |
| Rust | 12 | 86 | 98 |
| PHP | 16 | 57 | 73 |
| Python | 35 | 33 | 68 |
| Source: Applications monitored by Dependabot | |||
Stay secure while using open source
With so many dependencies it’s inevitable that security vulnerabilities creep in, and any one of them could be critical. Thankfully, GitHub’s Security Alerts help automate the process of monitoring your dependencies for vulnerabilities. With Security Alerts in place, GitHub sent over 10 million alerts to projects, related to over 1,000 vulnerabilities in 2018.
Along with automating your monitoring process, we introduced the Dependabot app to help check for security advisories in dependency files. Dependabot automatically creates pull requests in response to security advisories. Every day it pulls down your dependency files, parses them, and checks for any out-of-date or insecure dependencies. If it finds any it creates a pull request on GitHub, isolating the specific dependency that needs updating, with details of what has changed.
Stay up-to-date with new releases
Dependabot doesn’t just create pull requests for security vulnerabilities—by default, it will create pull requests whenever an update is available. This brings an iterative approach to dependency management.
To help ensure those newly created pull requests are easy to merge, Dependabot shares the CI pass rate for all projects performing the same update using a badge on the pull request. For example, in a pull request updating Rails from 5.2.1 to 5.2.1.1 Dependabot reports that the update was passing CI on 97% of projects. With this information, you can merge with more confidence, and also see how other (open source) projects are dealing with any breaking changes.
Wondering how much work it is to stay up-to-date? A typical ruby project (with 38 top-level dependencies) normally receives two dependency updates a week. Of those updates, 94% are non-breaking, which means that on average you’ll only need to write any code in response to a dependency update once every two months. The rest of the time you can just click “merge” and work with secure, up-to-date dependencies.
Check out Dependabot on GitHub Marketplace
Tags:
Written by
Related posts
GitHub recognized as a Leader in the Gartner® Magic Quadrant™ for Enterprise AI Coding Agents for the third year in a row
We are committed to empowering every developer by building an open, secure, and AI-powered platform that defines the future of software development.

Improving token efficiency in GitHub Agentic Workflows
Agentic workflows that run on every pull request can quietly accumulate large API bills. Here’s how we instrumented our own production workflows, found the inefficiencies, and built agents to fix them.
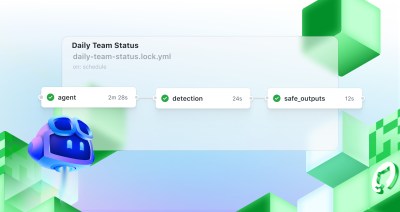
Automate repository tasks with GitHub Agentic Workflows
Discover GitHub Agentic Workflows, now in technical preview. Build automations using coding agents in GitHub Actions to handle triage, documentation, code quality, and more.